To accomplish the mammoth task of informing about 50 different vendors and various ISPs we teamed up with CERT/CC (VU#566724). We would really like to report that our efforts were successful, but as it turns out the number of devices on the web using known private keys for HTTPS server certificates has gone up by 40% in the last nine months (3.2 million in November 2015 vs. 4.5 million now). There are many explanations for this development. The inability of vendors to provide patches for security vulnerabilities including but not limited to legacy/EoL products might be a significant factor, but even when patches are available, embedded systems are rarely patched. Insufficient firewalling of devices on the WAN side (by users, but also ISPs in case of ISP-supplied customer premises equipment, CPE) and the trend of IoT-enabled products are surely a factor as well.
In our initial study we analyzed SSH host key use as well. Unfortunately there is no recent scan data on SSH host keys available (however there is a ticket over at the awesome ZMap project).
In the spirit of open research we are releasing the raw data today on Github. The data we are publishing consists of 331 certificates including the matching private key as well as 553 individual private keys. We’ve also included the names of products that contain the certificates/keys. Cryptographic keys that were not found in Internet-wide scan data (Scans.io and Censys.io, HTTPS/SSH) are included as well. These might be used in other protocols such as EAP/802.1X, FTPS etc. The data we are publishing allows researchers to reproduce the results of our study, find more cases or cryptographic key reuse, attribute cryptographic keys to specific vendors/products, but also to develop tools for detecting and exploiting this vulnerability class in the course of penetration tests. Releasing the private keys is not something we take lightly as it allows global adversaries to exploit this vulnerability class on a large scale. However we think that any determined attacker can repeat our research and get the private keys from publicly available firmware with ease.
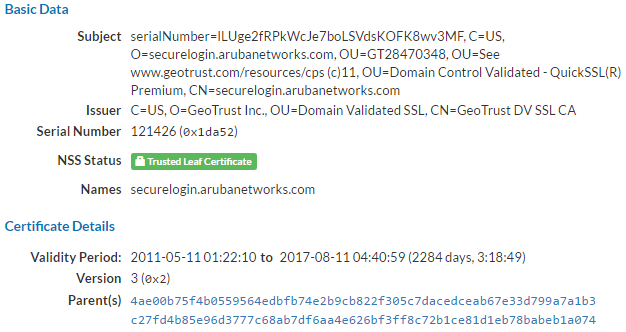
Some highlights from the data set were already mentioned in our initial blog post last year, including our beloved Broadcom SDK “Daniel” certificate, that is still used by 500.000 devices, or the Multitech/Texas Instruments certificate that is used by 280.000 devices on the web.
Our upcoming IoT/CPE firmware security analysis solution for device vendors and ISPs detects cryptographic key reuse vulnerabilities.
Ubiquiti Networks
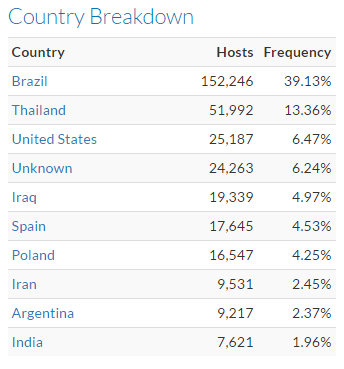
Last year we published a blog post titled The Omnipresence of Ubiquiti Networks Devices on the Public Web in which we discussed why so many Ubiquiti Networks devices are on the public web. In this case we can report some improvement. The number of devices on the web has gone down by 62% (1.1 million in November 2015 vs. 410.000 now). The bad news is that the major drop is likely caused by various botnets that exploit weak credentials as well as critical vulnerabilities including an innocently titled “Arbritrary file Upload” vulnerability (straightforward remote code execution, Metasploit module available). These botnets might have forced Ubiquiti customers to firewall their devices. Symantec has released a report on one of the malware families.