IT Infrastructure Security
IT Infrastructure Security deals with a broad range of devices and corresponding configurations and with necessary concepts for everyday operations. SEC Consult monitors your hardware, software, appliances and operating systems for weaknesses and ensures optimal protection for your business.
For an entirely secure infrastructure
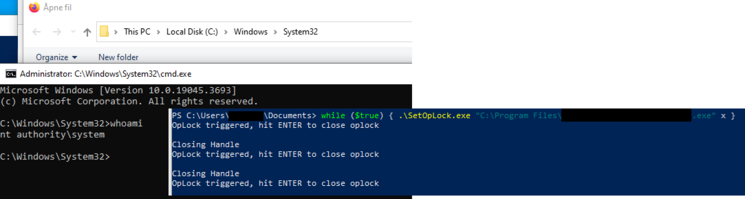
Weakness manufacturing instead of exclusively automated tests
Automated methods are only employed in SEC Consult’s IT Infrastructure Security Service to identify “low hanging fruits”. Our security experts mainly use manual methods to identify critical weaknesses. This results in a high level of detail of analyses and high-quality results, which reveal actually exploitable weaknesses and exploits.
Complex linking of attacks instead of simple attacks
Identification of an elementary weakness is not the end of the line at SEC Consult. By linking gateways, our experts can reveal complex attack routes and scenarios, which would not be visible in the event of documenting individual weaknesses.
Customized countermeasures and recommended actions
Illustrating points of attack is one thing. But the most important work only begins later. SEC Consult doesn’t just reveal weaknesses, but also works with you to find customized countermeasures to meet your needs, which can also be reasonably implemented in the environment being tested.
IT Infrastructure Security Projects
- Integrated approach
- Internal and external perspective
- Hardening existing infrastructure
- Design of future secure infrastructure
IT Infrastructure Security – where are the gaps?
- Has your external and/or internal network and server landscape grown over the years and you don’t have an overview of the current state of IT security?
- Do you want to know whether your network structure has been implemented correctly with regard to segmentation and filtering and complies with best practice?
- Are you currently introducing new operating systems and clients at your business or converting to “bring your own device” (BYOD) and Cloud Device Management, and don’t know whether your devices comply with the latest best practice?
- Do you operate a specialized infrastructure (payment handling, smart grids, smart building) and have to arrange for checks on these networks, for compliance reasons, to identify any gaps?
- Do you want to arrange for checks on the effectiveness of your new security solutions and appliances (IDS, IPS, WAF, Endpoint Protection, PAM, etc.)?
SEC Consult has compiled a comprehensive bundle of measures for this extensive and varied package of requirements.
We are happy to present the most important subjects:
SEC Consult counteracts the complexity of the threat scenario with integrated access, as a network offers virtually an infinite number of points of attack: guests and internal WLANs, physical access control systems, legacy services and networks, printers and fax machines, proliferation of operating systems, an uncertain standard configuration, VOIP telephony and conference systems, obsolete and forgotten servers, flat networks and the so-called demilitarized zone (DMZ) for direct external contact, … and much more. Many attack vectors should be noted from all possible directions and areas.
SEC Consult’s experts look at a business structure as a whole – or, if required, parts of it – both from the perspective of IT Security and with a view to potential attackers. As a result they provide an overview of your internal and external infrastructure and support you in protecting devices and configurations from all sides.
With the findings from monitoring, SEC Consult’s security experts work with you to develop measures to protect your existing infrastructure and prepare for attacks.
The measures developed with you by SEC Consult’s IT Infrastructure Security Team are individually customized in the same way as the IT infrastructure is individual at each company and organization. This also belongs to the view of the future and you will learn the necessary steps with regard to IT security in the design of your future infrastructure.
SEC Consult offers a range of security service packages to help organizations build a secure home office infrastructure.

DDoS protection for infrastructure
DDoS (Distributed Denial of Service) attacks cause significant material damage. To protect the availability of critical business processes and fullfill regulatory requirements such as DORA, ITSG, KRITIS-V, BSIG, DSGVO, TISAX and VAIT our experts check your DDoS resilience by performing a stresstest.
SEC Consult supports you with:
- Infrastructure DDoS (Layer 3 and 4)
- Application DDoS (Layer 7)
- Custom tests
- Proof of performance for compliance requirements according to legal regulations (e.g. DORA)
Protecting the availability of critical business processes
We work with you to create a business continuity plan. Our experts use a holistic approach that includes red teaming, web application and mobile security, and OT security.
Fulfillment of regulatory requirements in DORA and more
SEC Consult supports you in meeting necessary compliance requirements. The EU regulation on digital operational resilience in the financial sector DORA must be implemented by the companies concerned by January 17, 2025. They must then have a proven ability to detect and defend against cyberattacks. Our SEC Consult experts will be happy to support you in achieving and sustainably securing this goal.
Effective disaster recovery
DDoS stress testing is an essential tool to get your business or organization ready for a quick return to normal operations. In case of an emergency, SEC Consult's cybersecurity experts also take care of damage limitation and the prevention of a renewed attack and support you in strengthening your critical business processes with preventive measures.