Penetration Testing
A pentest is a quick, easy to plan, and – most importantly – affordable security audit to determine the security of systems at a given time.
If you are new to pentesting, during your initial consultation our SEC Consult expert will talk you through the process in order to help you define your best timeline and budget. According to the then predefined timeline, you will decide the level of depth you wish us to investigate and which scenario to focus on (e.g. targeted phishing emails). Critical vulnerabilities are generally the les easy to find.
As such, investigating every layer of code is essential. Keep in mind that the overall objective of a pentest isn’t to just look over everything superficially and confirm that at first sight all looks good. Most customers want to find what is not so obvious but can have a huge impact down the line of their organization.
Talk to our pentest specialists

Are all pentests created equal?
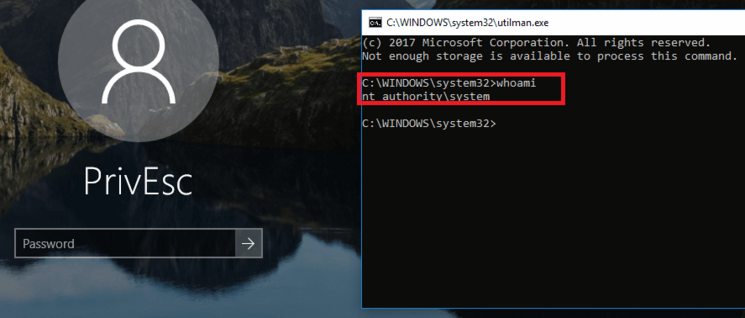
For every request, a pentest. While the goal to penetrate a system in a certain scope might be the common intention, depending on the amount of information provided and the accuracy of that information, each conducted pentest will be customized. When pentesting “blind” – aka “Black Box” testing – the tester has no previous knowledge of the testing environment and would act as your common hacker according to public information available.
In case of “White Box” testing, the hacker – thanks to an insider’s help or information gathered by a previous hack- will gain access to a complete set of documents including accounts with advanced privileges prior to his attack. Combine the two approaches, and we say the pentests are conducted in a “Grey Box” environment. Arrange a complimentary consultation with our Pentest experts.
Typically, pentests are performed on individual systems in the course of acceptance tests immediately before going live.
Afterwards, pentests should be repeated periodically as part of information security management, ideally based on each other and decoupled from the release cycle.
Just before commissioning a system just to comply with legal compliance, a pentest often puts more stress and problems into the project than at an earlier point in the project. Especially if there were no security checks before and the last project phases are usually very hectic even without a pentesting.
In addition, vulnerabilities found can sometimes be so critical that they need to be rectified immediately. In the case of security risks in architecture, this can in the worst case be a new development.
Time and Money
The more complex and critical the application, the higher the budget for the pentest. When establishing your budget, bear in mind that a security audit requires a certain amount of configuration and coordination efforts before testing even starts.
A system with financial data relevant to financial transactions should (hopefully) have a larger budget than the canteen’s static HTML website.
Know-how
Any skilled attacker would put all his effort and expertise to work, to find your sweet spot. In average, pentesting a web app might be done in a couple of days while pentesting a customer service helpdesk of a big telecom company might take weeks. In that case, size matters. A 360° pentest for a DAX company may easily last up to a three-digit amount of days. It really depends on the company and the project itself. Consider the criticality of your application, add the usual daily rates in the IT industry of your country and you have a rough estimate of what to expect.
SEC Consult conducts more than 600 pen tests worldwide every year. Particularly sensitive but recurring sources of error are, for example, database connections, login procedures, integration of external sources, central input and output validation.
A certain amount of information about the systems is available to the pentester during a penetration test. The range goes from no information – a so-called black box test – to complete documentation including adminstrator accounts with appropriate access rights – a so-called Whitebox test. All interpretations of the level of detail in between are called Greybox Test.
Thanks to the company’s in-depth expertise gathered over the years and over 800 pentest audits performed every year, SEC Consult has been able to developed an enhanced pentesting method, the “Glass Box”. Particularly sensitive areas are, for example, database connections, registration procedures, integration of external sources, central input and output validation and much more. By giving access to the source code, it offers the best depth-to-effort ratio for optimized results.
What is a glass box test?
The vast experiences across all manner of customers, technologies and breaches have led SEC Consult to the development of the “Glass Box” test. In order to carry out the most detailed risk analysis possible, the pentester is proviced with as much information about the application beforehand. Ideally, auditors have complete information about the application and even the source code of the relevant parts within a set scope.
A Glass Box security audit is a pentest with a manual review on the most safety-critical parts of the scope of the associated source code. Among the particularly sensitive parts, we find database connections, login procedures, integration of external sources, central input and output validation. This procedure offers a very high quality of results according to clearly established costs.
The majority of pentesting offerings on the market are related to the exploitation of known vulnerabilities thus concentrating mainly on known breaches. But new previously unknown vulnerabilities in your information system may result in its emergency shutdown or loss of data until remediation is complete. A SEC Consult pentest will also uncover previously unknown, undocumented vulnerabilities known as zero-day vulnerabilities.
Sometimes a technical patch is needed, sometimes the flaw is a consequence of an organizational shortcoming. By investing into regular security assessments and continuous training of their employees, technology-driven and security-aware companies aim to minimize the amount of critical risks, a crucial issue in the early stages of design and development.
How about a real-life example?
On any ERP-System, an intruder is not only able to extract corporate secrets, but can also gather and disclose employees, customers and partners’ sensitive information. Consequently, the targeted organization would not only have to face a large amount of privacy complaints but also a PR nightmare. The damages may not stop at theft and disclosure though, a skilled hacker might also be tempted (or paid) to manipulate entries in your database such as mutually agreed contract details, retail pricing and discounts. When such corruption comes to light, if it ever does, the ripple effect might have disastrous consequences on your organization and/or your own career.
Other examples from everyday life include quick-pay terminals at supermarkets and charging stations, smart locks and smart home technology in general. It is the vendor’s responsibility to not only provide secure products and their implementations, but also to make the users aware of potential risks, linked to default/weak passwords, internet-accessible configurations, etc., when using this technology.
In an ideal world – where practical pen tests are employed in logical phases: execute the first pentest after the prototype or staging of the Minimum Viable Product. The second phase is then carried out after finalization of the release candidate and a recheck can be added in the production environment before going live. This phased approach represents Best Practice in the industry and is proven to be the most cost-effective method for minimizing risks associated with application development.
As you may guess from its name, a pentest is a specialized type of information security assessment that inspects how a technology (applications, software components and infrastructure) can be infiltrated by simulating a cyberattack. Expert security practitioners use purpose-built tools and procedures to identify vulnerabilities that can be dormant and undetected simply because software developers and vendors have other goals and employ a different way of thinking than a motivated and skilled hacker.
Today, penetration testing (in short: ″pentesting″) has become a well-established best practice. While this approach was common practice a few years ago, especially in IT-heavy industries such as the finance or telecommunications sectors, pent-up development is advisable or even necessary for all sectors as digitalization progresses.
The goal is to find as many security relevant configuration issues and known vulnerabilities as possible, in addition to previously unknown security issues (so called zero-day vulnerabilities), as in a set amount of time. This approach is called a “timebox” and is generally based on budget, timing and process.
A real attacker does not necessarily stop after infiltrating a certain technology. Personal, classified or other data worth protecting are his grail before he turns to installing malware and gathering all the worthwhile resources he can for later exploit. Needless to say, all of which could jeopardize your company’s image and lead to severe financial and reputational loss.
It is advisable to provide the pentester with sufficient time and to repeat pentests at certain intervals. After several thousand penetration tests, it is clear that there is “always something to be found”.
Non-functional requirements
As security is a non-functional requirement, the service or software may work as designed on its own but still contain a large amount of vulnerabilities that make its use dangerous for any service provider and/or user. These vulnerabilities can originate from the software product itself or result from of misconfiguration of the underlying infrastructure. A pentest reveals what could possibly go wrong in the case of an attack. Every organization, regardless of its size, that processes data or uses digital methods of communication is prone to such a cyberattack. In a digital world like ours, the question arising is then not IF there will be an attack but WHEN.
The BSI (German Federal Office for Information Security) has the task of advising and supporting operators of critical infrastructures at their request in securing their information technology. Particularly in the case of targeted attacks by highly professional adversaries (Advanced Persistent Threat, APT), special requirements must be met by the respective service providers. For this reason, the BSI maintains a list of recommended companies with proven qualifications and suitability in this area.
SEC Consult Germany and ATOS Cybersecurity Germany have a - globally unique - selling proposition of certificates and qualifications.
Together, both are the only company that:
- Qualified APT response service provider of the BSI AND
- CREST Cyber Security Incident Response certified AND
- Is a BSI testing center for penetration testing, IS auditing and IS consulting.