Management summary
An incomplete authorization check in Open WebUI allowed low privileged attackers to access sensitive Tool data.
Vendor description
"The self-hosted AI interface. Open WebUI is the platform for running AI on your own terms. Connect to any model—local or cloud. Extend with Python. Share what you build with 331K others. 270 million downloads and growing."
Source: https://openwebui.com/
Business recommendation
The vendor provides a patch which should be installed immediately.
SEC Consult highly recommends to perform a thorough security review of the product conducted by security professionals to identify and resolve potential further security issues.
Vulnerability overview/description
1) Broken Access Control in Tool Valves (CVE-2026-34222)
Open WebUI supports function calling through "Tools". Function calling allows an LLM to reliably connect to external tools and interact with external APIs. Exemplary use-cases include connecting to an internal knowledge base, retrieving emails from an exchange server, or retrieving order data from a shop backend. These interactions often require the LLM to authenticate against backend services using API keys specifically created for a technical (Open WebUI) user.
To simplify configuration and secret handling, Open WebUI implements "Valves" and "UserValves" that allow users and administrators to input dynamic details like API keys or configuration options.
Valves have the following distinction:
- Valves: Configurable by admins only.
- UserValves: Configurable by any user.
The Tool Valves endpoint does not properly restrict read access to the valve. This allows a low privileged user to access all data contained within the valve. In the worst case, this gives a low privileged "Member" user access to sensitive Tool data, such as API keys for third-party systems.
Proof of concept
1) Broken Access Control in Tool Valves (CVE-2026-34222)
The following steps can be performed to reproduce the vulnerability.
1. An administrator creates an Open WebUI Tool with a configured Valve.
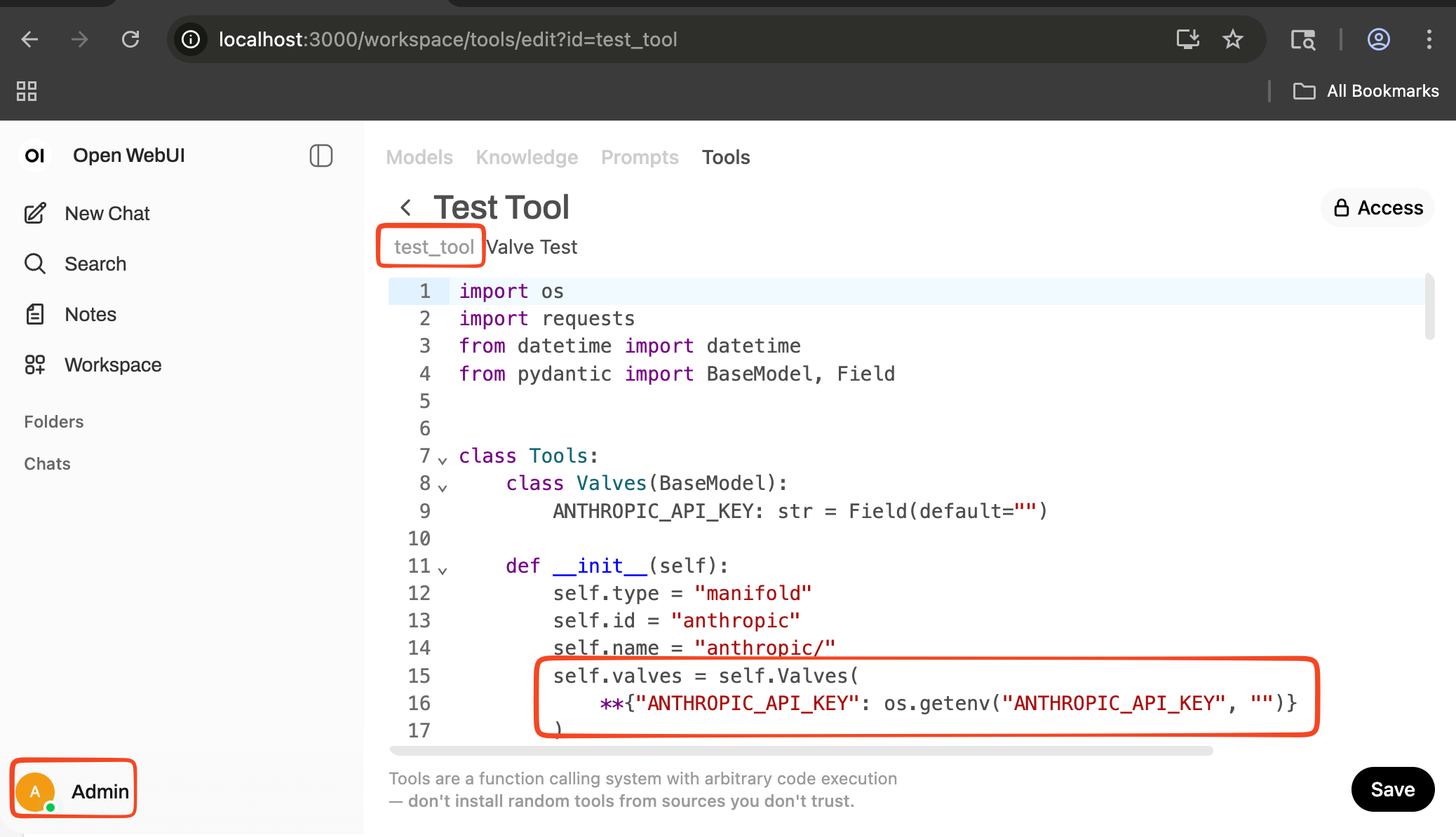 Figure 1: Open WebUI Tool with a configured Valve
Figure 1: Open WebUI Tool with a configured Valve
2. The administrator configures the API key within the Tool Valve.
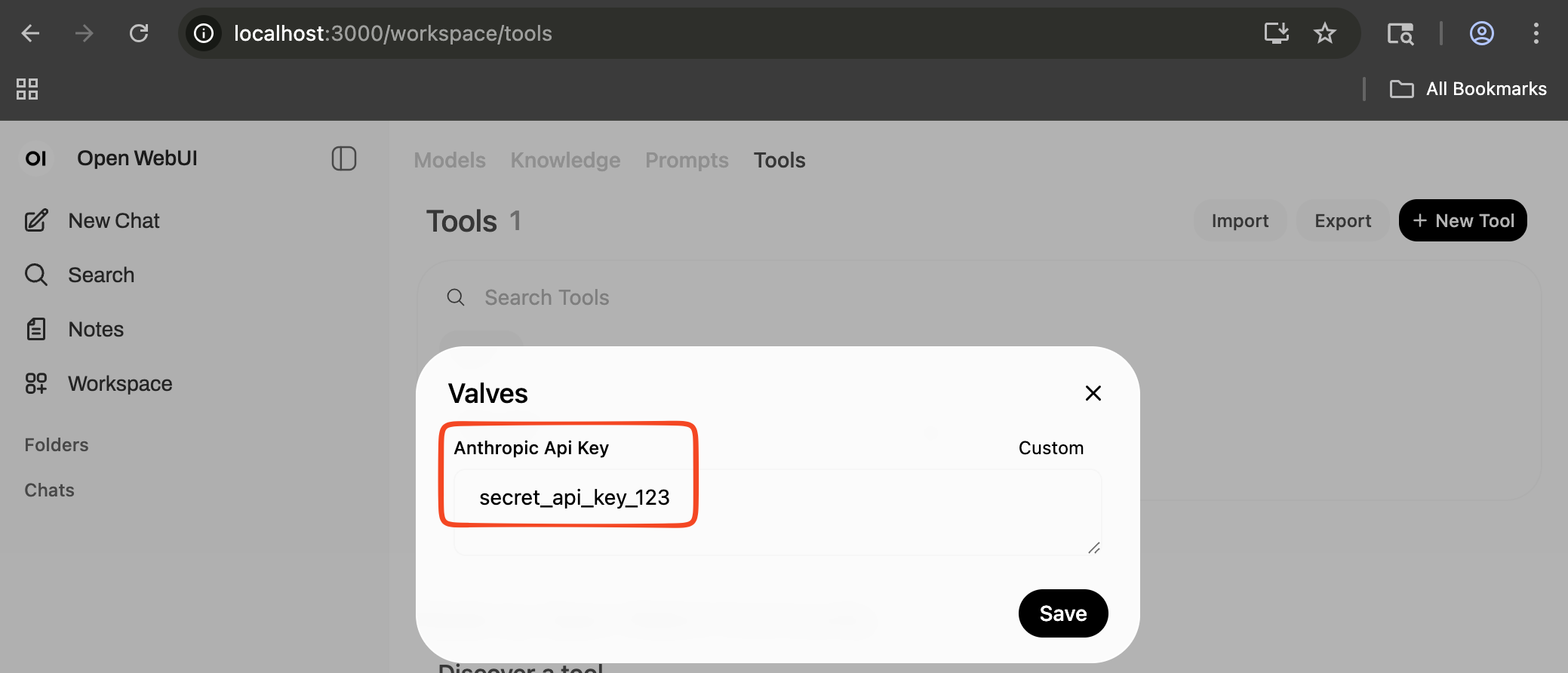
Figure 2: API key
3. A user with at least "Member" privileges logs into Open WebUI.
The following screenshot shows the user overview of the test instance:
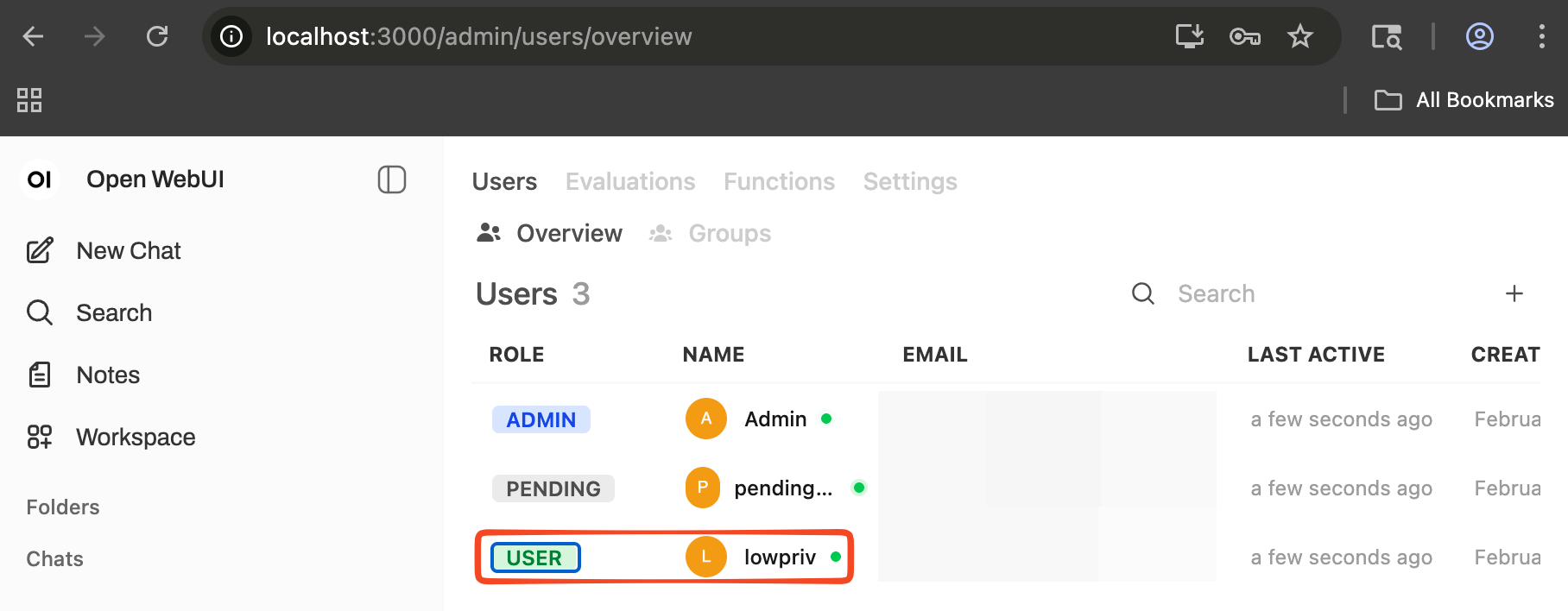
Figure 3: User overview
The following screenshot illustrates that the "lowpriv" user doesn't have access to the tool:
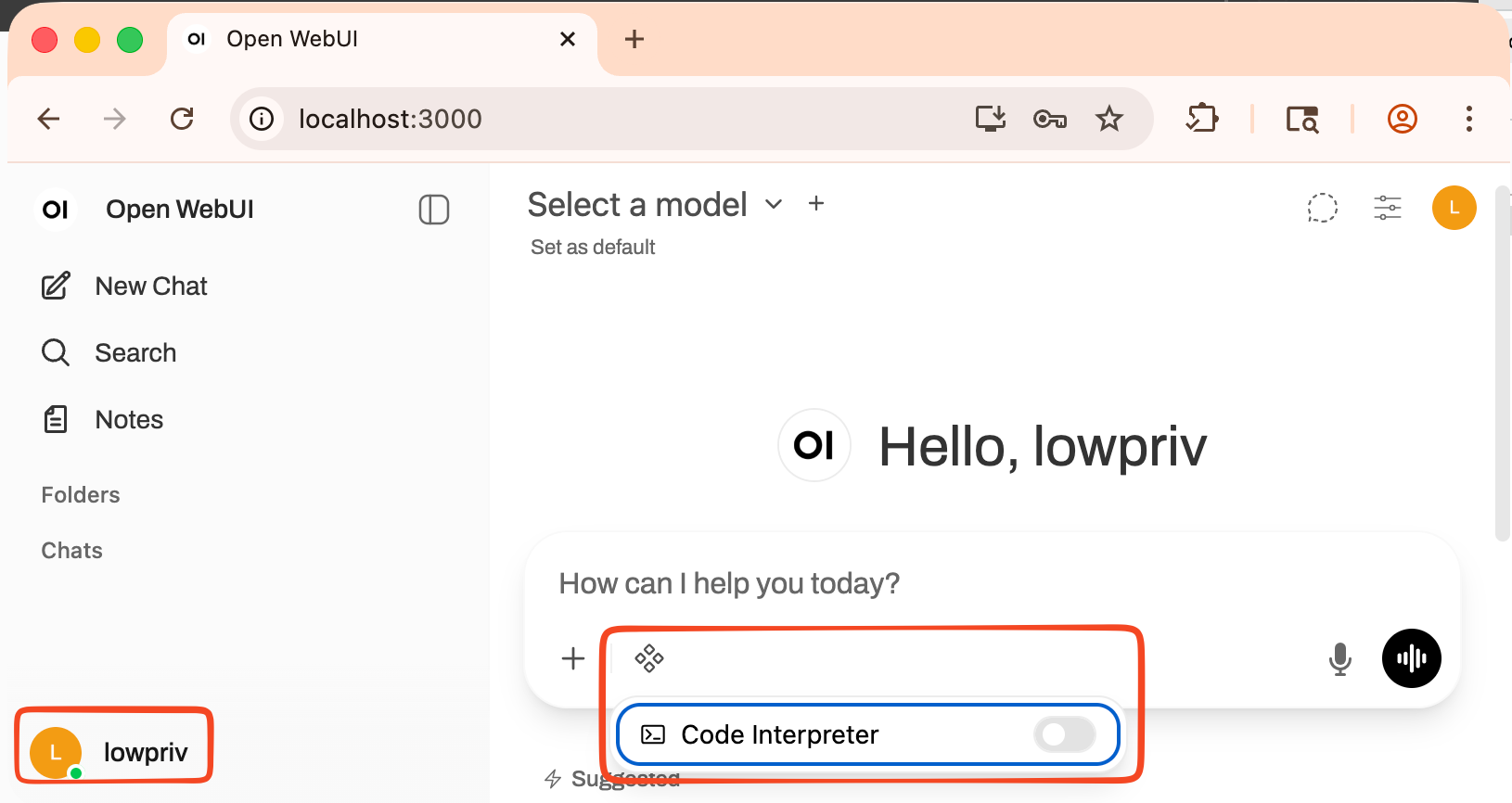
Figure 4: Low-privileged user has no access
4. The "lowpriv" user uses their Authorization token to retrieve the API key from the Tool Valve.
In order to do so, the attacker needs to know the Tool ID. However, as this ID is always the same for imported tools, and the tool IDs are concatenated from the tool name, guessing tool IDs is trivial.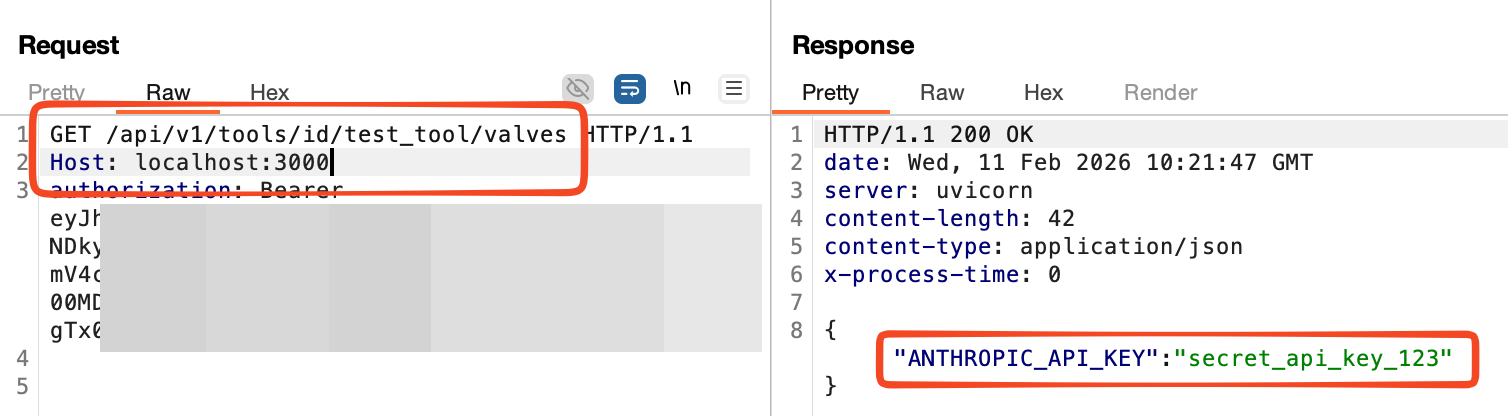
Figure 5: Authorization token used to obtain API key
As seen in the following code snippet, the vulnerability is present because the Tool Valves route does not check if the requesting user has administrative permissions.
@router.get("/id/{id}/valves", response_model=Optional[dict])
async def get_tools_valves_by_id(
id: str, user=Depends(get_verified_user), db: Session = Depends(get_session)
):
tools = Tools.get_tool_by_id(id, db=db)
if tools:
try:
valves = Tools.get_tool_valves_by_id(id, db=db)
return valves
[...]
)Vulnerable / tested versions
The following version has been tested which was the latest version available at the time of the test:
- v0.7.2
All versions below the fixed version v0.8.11 are affected.