The password of database connections in Amazon AWS Glue is loaded into the website when a connection's edit page is requested. Principals with appropriate permissions can read the password. This behavior also increases the risk that database passwords will be intercepted by an attacker during transmission in the server response. Many types of vulnerabilities, such as broken access control, cross-site scripting and weaknesses in session handling, could enable an attacker to leverage this behavior to retrieve the passwords.
Vendor description
"AWS Glue is a serverless data integration service that makes it easier to discover, prepare, move, and integrate data from multiple sources for analytics, machine learning (ML), and application development."
Source: https://aws.amazon.com/glue/
Business recommendation
The vendor has fixed the issue in the currently available version on all instances world-wide as of 2024-02-23.
Vulnerability overview/description
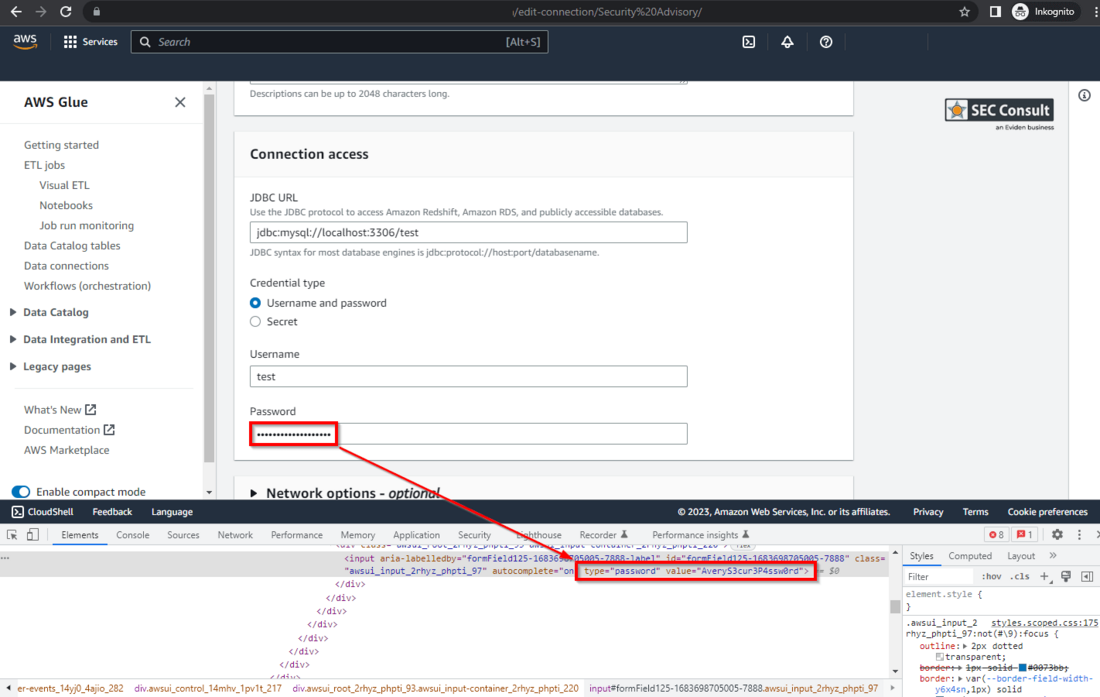
1) Database Passwords in Server Response
The password of database connections in AWS Glue is loaded into the website when a connection's edit page is requested. Principals with appropriate permissions can read the password. This behavior also increases the risk that database passwords will be intercepted by an attacker during transmission in the server response. Many types of vulnerabilities, such as broken access controls, cross-site scripting and weaknesses in session handling, could enable an attacker to leverage this behavior to retrieve the passwords.
Proof of concept
1) Database Passwords in Server Response
The following steps are necessary to reconstruct the vulnerability:
- Login to the AWS Console and switch to the Glue module.
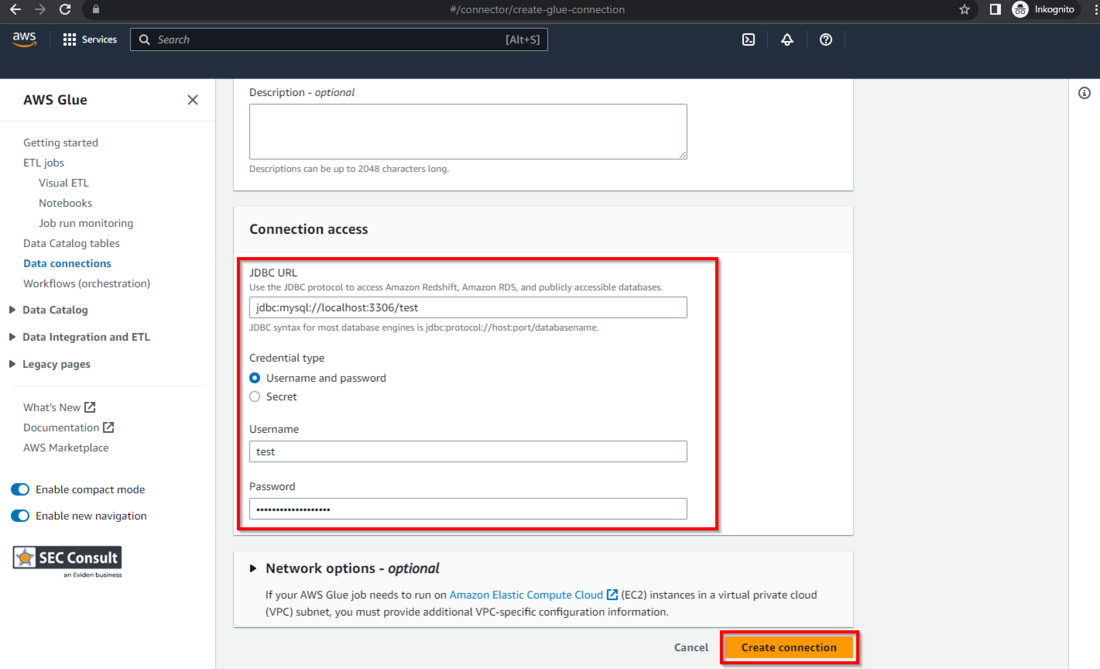
- Go to "Data connections" and create a new connection.
- Choose a connection type that allows username / password authentication (e.g. JDBC) - see figure 1.
- Open the new connection's "Edit" page and inspect the password field e.g. with the browser's DevTools - see figure 2.
The following permissions were used:
- glue:GetConnections (for the list view of connections; not necessary to open the connection page itself if the connection name is known)
- glue:GetConnection (for opening the connection page)
- ec2:DescribeSubnets (for opening the edit page of a connection)
Permission Summary
A principal only needs the permissions glue:GetConnection and ec2:DescribeSubnets to retrieve the database password of a connection. The attacker also needs either knowledge of the connection's name to open the edit page directly (e.g. us-east-1.console.aws.amazon.com/gluestudio/home) or the permission glue:GetConnections to list existing connections.
Vulnerable / tested versions
The version that was current at 2023-05-10 has been tested and found to be vulnerable.
Vendor contact timeline
Solution
The vendor has fixed the issue and deployed the patch worldwide as of as of 2024-02-23.
Workaround
None
Advisory URL
https://sec-consult.com/vulnerability-lab/
EOF Michael Werner / @2024
Interested to work with the experts of SEC Consult? Send us your application
Interested in improving your cyber security with the experts of SEC Consult? Contact our local offices