Management Summary
A missing TLS server certificate validation in CleverControl's "CleverControl" employee-monitoring application installer enables attackers, who can inject themselves into the network path between the client and the server, to execute arbitrary code with administrative privileges.
Vendor description
"Imagine a work environment where employee monitoring software empowers, not restricts. Where collaborative insights fuel optimizations and breakthroughs, and employee well-being stands hand-in-hand with shared success. This is the environment CleverControl brings to life. We're not about micromanagement. We're about unlocking team potential through powerful, ethical tools. Our employee monitoring software sheds light on workflow patterns, revealing trends, bottlenecks, and hidden growth opportunities, all while ensuring ironclad data security and encryption (in compliance with ISO 27001 Standard and stored on secure servers) and ethical usage policy."
Source: https://clevercontrol.com/
Business recommendation
The vendor was unresponsive and did not answer to our communication attempts. Therefore, a patch is not available for this security issue. End users of this product should contact the vendor and demand a patch.
SEC Consult highly recommends performing a thorough security review of the product conducted by security professionals to identify and resolve potential further security issues.
Vulnerability overview/description
1) Missing Certificate Validation leading to RCE (CVE-2025-10548)
When deploying the CleverControl MSI, two executables are downloaded without checking the validity of the server certificate. Those are then executed with SYSTEM rights. This enables an adversary-in-the-middle attacker to gain code execution with elevated privileges on the system.
Proof of concept
1) Missing Certificate Validation leading to RCE (CVE-2025-10548)
When the MSI installer file is opened with 7-zip, two script files, `instredist.cmd` and `srec.cmd` are revealed.
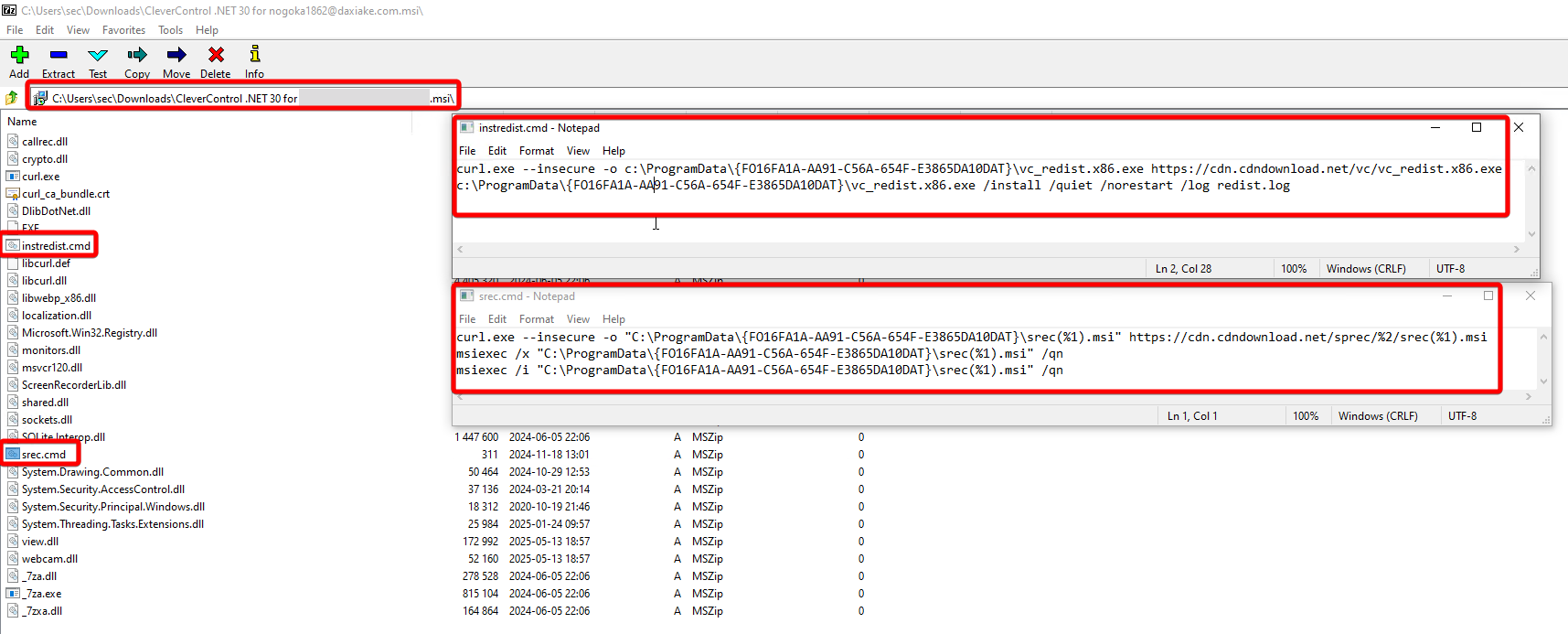
Figure 1: CleverControl update scripts
Contents of `instredist.cmd`:
curl.exe --insecure -o c:\ProgramData\{FO16FA1A-AA91-C56A-654F-E3865DA10DAT}\vc_redist.x86.exe cdn.cdndownload.net/vc/vc_redist.x86.exe
c:\ProgramData\{FO16FA1A-AA91-C56A-654F-E3865DA10DAT}\vc_redist.x86.exe /install /quiet /norestart /log redist.logContents of `srec.cmd`:
curl.exe --insecure -o "C:\ProgramData\{FO16FA1A-AA91-C56A-654F-E3865DA10DAT}\srec(%1).msi" cdn.cdndownload.net/sprec/%2/srec(%1).msi
msiexec /x "C:\ProgramData\{FO16FA1A-AA91-C56A-654F-E3865DA10DAT}\srec(%1).msi" /qn
msiexec /i "C:\ProgramData\{FO16FA1A-AA91-C56A-654F-E3865DA10DAT}\srec(%1).msi" /qnMonitoring the installation process with `ProcMon` shows that these scripts are indeed executed during the installation:
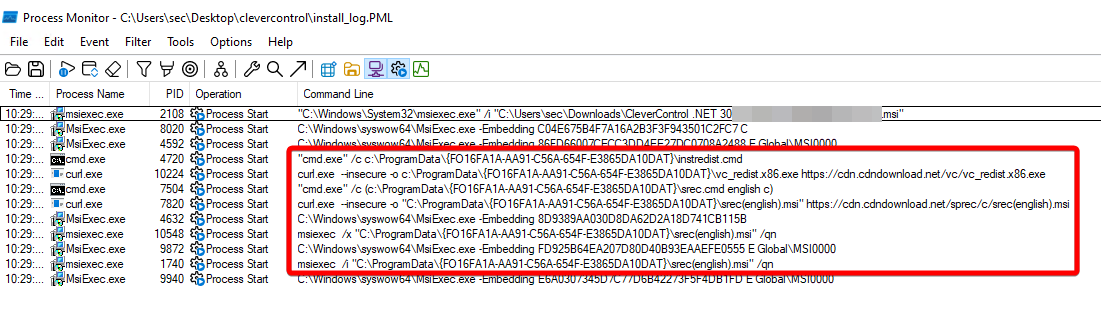 Figure 2: Procmon output
Figure 2: Procmon output
Because curl.exe is started with the `--insecure` flag, the TLS certificate of the server is not validated. This means that the TLS connection can be intercepted by an attacker with an adversary-in-the-middle attack.
Therefore, an attacker who can perform such an attack can respond with malicious files like `vc_redist.x86.exe` or `srec(english).msi` and execute malware with SYSTEM privileges.
This attack is demonstrated in the following animation which mimics an adversary-in-the-middle attacker by hard-coding the DNS resolution for `cdn.cdndownload.net` to point to localhost and by hosting the malicious file on localhost with `updog`. The malicious .exe file was generated with the following msfvenom command:
$ msfvenom -p windows/adduser USER=owned -f exe -o vc_redist.x86.exe