Vendor description
"Create your own individual Mobile App with Anveo. Our base, out of the box solutions offer many useful functions, and can be flexibly adapted to your requirements: the Anveo Service App, Anveo Sales App, and Anveo Delivery App. You are looking for a mobile App for a different scenario? Not a problem with the Anveo Mobile App Builder! Thanks to the toolkit character of the solution, configuration of a completely new, custom App is simple."
Source: https://www.anveogroup.com/en/mobile-apps-for-dynamics/
Business recommendation
The vendor was unresponsive and did not reply to our communication attempts and even deleted our comment to request a contact on LinkedIn, see the timeline section further below.
There is no solution known to us for this security issue. In case you are a customer of Anveo, request an update from them about the issue. Furthermore, an in-depth security analysis performed by security professionals is highly advised, as the software may be affected from other security issues.
Vulnerability overview/description
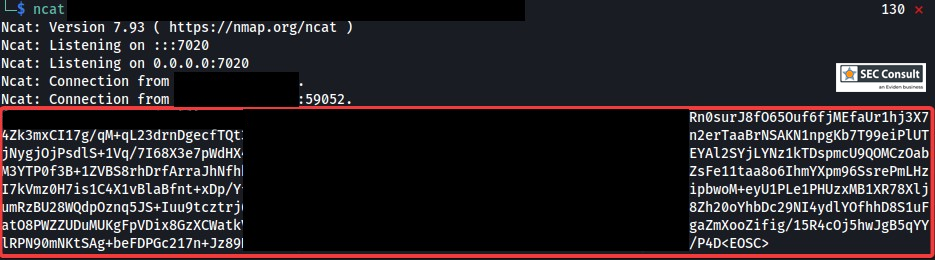
1) Missing Certificate Validation
The Windows application was tested which does not perform certificate validation and is therefore vulnerable to man-in-the-middle attacks which might allow an attacker to gain access to sensitive data.
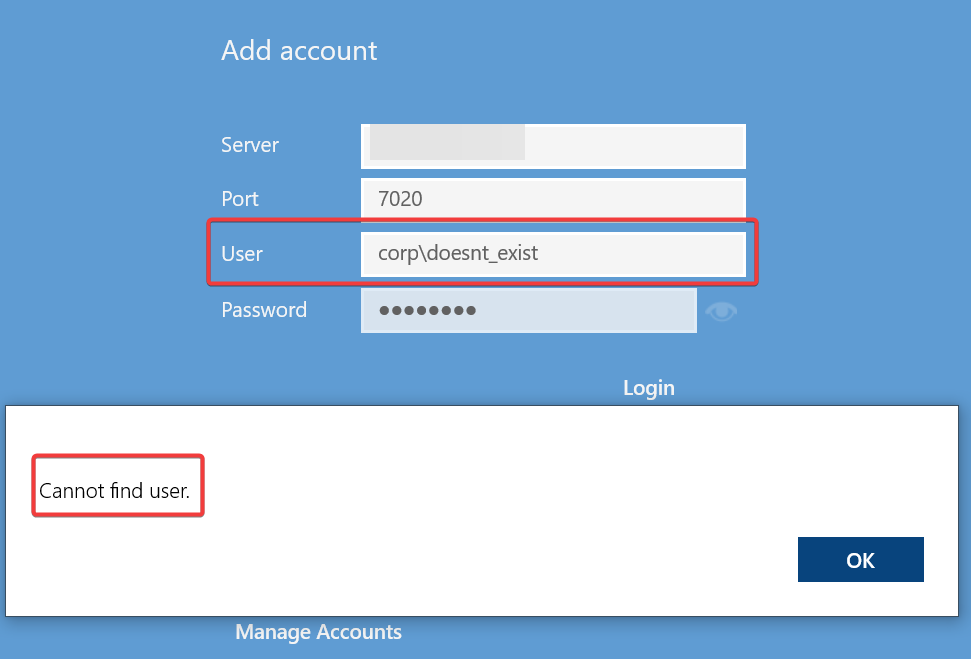
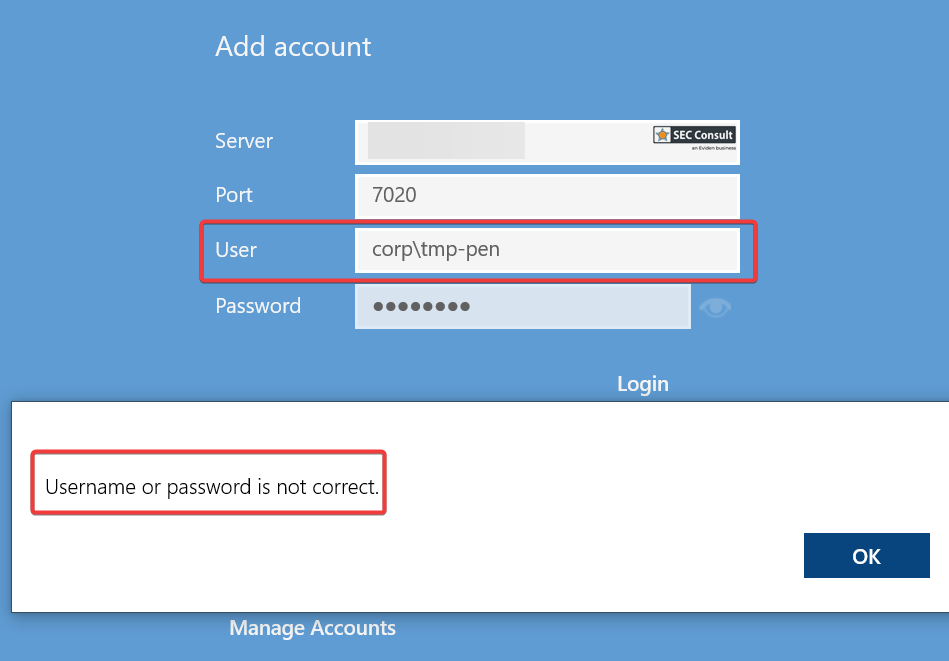
2) User Enumeration
The login is vulnerable to user enumeration because the error message for a non-existent user differs from the error message when a user exists. This allows an attacker to perform targeted brute-force attacks and potentially take over other user accounts.