Vendor description
"BMD develops high-quality business software and is one of the leading software manufacturers in Austria. But also many customers in Germany and Switzerland as well as in the international European region rely on the software solutions developed by BMD."
https://www.bmd.com/en/about-bmd/cdompany-profile.html
Business recommendation
The vendor provides a software update which should be installed immediately.
SEC Consult highly recommends to perform a thorough security review of the BMD Web product conducted by security professionals to identify and resolve potential further security issues.
Vulnerability overview/description
1) Stored Cross Site Scripting (Outdated software library)
BMDWeb 2.0 uses DOMPurify version 1.0.10 (released in Feb 19, 2019) for sanitizing untrusted user input. This outdated version suffers from many vulnerabilities that allow bypasses of the sanitization logic.
A few examples:
- https://github.com/cure53/DOMPurify/issues/482
- https://research.securitum.com/dompurify-bypass-using-mxss/
- https://research.securitum.com/mutation-xss-via-mathml-mutation-dompurify-2-0-17-bypass/
- https://portswigger.net/research/bypassing-dompurify-again-with-mutation-xss
An attacker can execute arbitrary JavaScript code in the context of the victim's BMD session, thus perform all actions in BMD, exfiltrate information, etc.
Note for DOMPurify users:
DOMPurify should be updated regularly. The project provides a mailing list with the latest security information.
Further information: https://github.com/cure53/DOMPurify#security-mailing-list
Additionally, input validation is another measure against Stored Cross Site Scripting.
Proof of concept
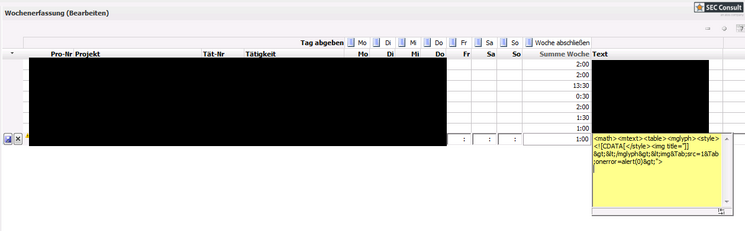
1) Stored Cross Site Scripting (Outdated software library)
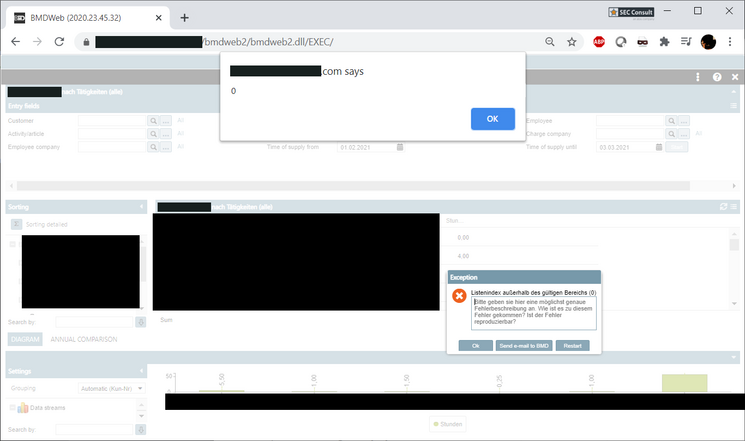
The following XSS vector can be used in all kinds of BMD user input fields, e.g. time recording comment, service entry comment, etc.
<math><mtext><table><mglyph><style><![CDATA[</style><img title="]]></mglyph><img	src=1	onerror=alert(0)>">This JavaScript code will then automatically get executed when the site which contains the payload is visited by the victim.