Technical Analysis
In order to understand how the phone number including the secret OTP that authenticates the user can be stolen by a malicious installed application, we first need to clarify what "Intents" in Android are.
What are Intents in Android?
Intents are a fundamental component of Android, enabling messaging between various components of an application or even between different applications. They serve as a fundamental building block of the Android operating system and play a crucial role in enabling various functionalities and interactions.
An intent can be viewed as an abstract description of an operation to be performed, typically consisting of two essential components: the action and the data. The action represents the type of operation to be performed, such as "view", "edit", or "send". The data, on the other hand, specifies the content or target of the operation, such as a specific URL, a file, or a piece of data.
Types of intents in Android
Explicit Intents: An explicit intent is used when the developer knows the specific target component (e.g., an activity, service, or broadcast receiver) that should handle the intent. It explicitly specifies the target component's class name or package name, ensuring a direct and specific delivery.
Implicit Intents: An implicit intent is more flexible and allows the system to determine the appropriate component to handle the intent based on its action and data. Implicit intents are useful when developers want to delegate a task to another component without specifying the exact target component. For example, if an application wants to share an image, it can create an implicit intent with the ACTION_SEND action and the image's data, allowing the user to choose from a list of available applications to handle the sharing operation. If only one application that can handle the specific intent action is installed on the device, the operating system will automatically choose it without user interaction.
Intents are not only used for launching activities or services within an application but also for inter-app communication. They enable developers to leverage functionalities provided by other applications by sending intents with appropriate actions and data. This inter-app integration empowers developers to create rich and interconnected user experiences.
Overall, intents in Android serve as a versatile mechanism for communication and coordination between different app components and enable seamless interactions, data sharing, and inter-app integration.
Use-cases
Intents in Android have various use cases and are a fundamental part of inter-component communication. The following is just an excerpt:
Starting Activities: Intents are commonly used to start activities in Android. By creating an explicit or implicit intent with the appropriate action and data, developers can launch activities within their own app or in other apps. For example, clicking a button to open a new screen or launching the camera app to capture a photo.
Service Invocation: Intents can be used to start or interact with background services in Android. Developers can create an intent to start a service and provide necessary data or commands for the service to execute. This is useful for long-running background tasks, such as downloading files, playing music or performing computational intensive tasks without freezing the UI.
Broadcasting Events: Intents are used for broadcasting events or messages across different components or apps. By broadcasting an intent, developers can notify interested receivers about certain events or trigger actions. For example, sending a broadcast intent to notify other apps about the device's network connectivity change or battery level.
Intent Broadcasts
As mentioned, intents can be broadcasted. To interact with such an intent, a BroadcastReceiver can listen for them and respond appropriately. Broadcasting an intent is like shouting out a message for anyone interested to hear. Any component that's interested in receiving that message can register a BroadcastReceiver with the system to listen for that particular message.
Intent broadcasts are often used for various purposes in Android development, such as system events (e.g., device boot completion), notifying components about changes (e.g., network connectivity, battery status), sending notifications to multiple receivers, or triggering custom events within an application.
Security Considerations
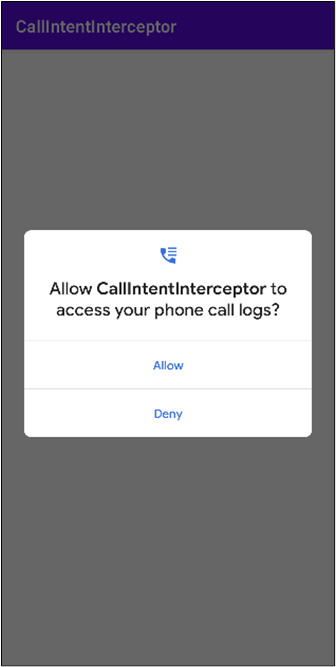
Implicit broadcast intents in Android are of special interest when they are supposed to be used for transporting (sensitive) data to other app components or apps, since they can be intercepted and received by unintended or malicious applications. When an implicit broadcast intent is sent, it is not explicitly targeted at a specific application but rather broadcasted to all applications that have registered to receive that particular type of intent. This can potentially lead to unintended exposure of sensitive information or unauthorized access to certain functionalities.
For example, if an implicit broadcast intent containing sensitive data, such as user credentials or personally identifiable information, is sent, any application with the appropriate permission can intercept and access that information. Malicious apps can exploit this by registering to receive the same intent and retrieve sensitive data without the user's knowledge or consent.
Furthermore, implicit broadcast intents can be used to trigger unintended actions or disrupt normal app behavior. Malicious apps can register to intercept and cancel certain broadcast intents, leading to unexpected consequences or denial of service attacks.
Dual-Tone Multi-Frequency (DTMF) Signaling
In the high-level vulnerability description we mentioned that the generated OTP is appended to the phone number. This is actually not completely true. Instead of simply appending it to the phone number, it is transmitted to the banking system using DTMF signaling.
DTMF allows users to input numeric or alphanumeric characters using their phone's keypad while engaged in a phone call. When a user presses a digit on their phone's keypad, it generates a unique combination of two specific frequencies, known as dual-tone multi-frequency signals. Each digit corresponds to a specific pair of frequencies. These signals are transmitted over the voice channel of the phone call and decoded at the receiving end. DTMF signaling is widely used for various purposes, such as automated phone systems, interactive voice response (IVR) systems, phone banking, entering passwords or PINs, conference call access codes, and menu navigation within voice-based systems. The receiving end, typically a telephone exchange or a computer system, decodes the DTMF signals and processes the entered digits accordingly. This allows users to interact with automated systems, enter numeric inputs, or navigate through menu options during a phone call. DTMF signaling has become a standard method for inputting digits during phone calls and is supported by most modern telecommunication systems and devices, including landline phones, mobile phones, and Voice over IP (VoIP) services.
The call intent used to initiate the call to the banking hotline already includes the OTP which authenticates the user via DTMF Signaling.