NIS2
We support your company in meeting the legal and technical requirements of the NIS2 directive. Through expert advice and strategic solutions, we sustainably improve cyber security in your relevant network and information systems. In this way, we ensure that your business is optimally aligned and prepared for NIS2.
NIS2 is the second version of the Network and Information Security Directive, which regulates the security requirements for operators of essential services and digital service providers in the European Union. It significantly expands the previous NIS scope of application, places more extensive requirements on risk management and incident reporting and provides for stricter enforcement measures.
Directive with implementing legislation in each EU member state
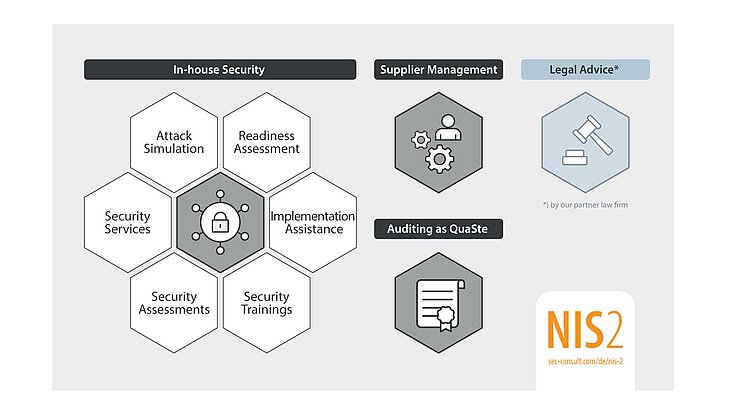
NIS2 consulting from a single source
The modern landscape of information security laws and regulations can be overwhelming, especially for smaller organizations. We can help you understand cybersecurity requirements and identify associated measures to ensure compliance with NIS2 regulations.
Once we have jointly defined the scope of the project, a thorough gap assessment will be conducted against NIS2 requirements and industry standards. A customized compliance strategy is then developed, followed by the creation of a detailed project plan with cybersecurity measures.
We provide ongoing support, including access to templates, from our cybersecurity experts. Internal or “QuaSte” audits ensure ongoing compliance, complemented by due diligence reviews from professional legal experts. By taking these steps, you can efficiently improve your cybersecurity posture and meet your NIS2 obligations.
Many years of experience
SEC Consult and Eviden have extensive knowledge in the implementation and auditing of information security management systems according to common standards such as ISO 27001 or VDA ISA 5.x and 6.x. To ensure that your company achieves the best results, our services are tailored precisely to your needs.
Multidisciplinary team of experts
Our team offers experts from all areas of cybersecurity: infrastructure, governance, risk and compliance, applications, OT or IoT systems, SAP or incident response. This enables us to ensure the best results for our customers.
QuaSte
SEC Consult has been accredited as a “Qualified Body” since 2021 and has since carried out numerous audits in a wide range of industries. Through close communication with authorities and interest groups, we can optimally align our services to the legally compliant level.
NIS2 Whitepaper
Our white paper provides a clear and understandable overview of the NIS2 Directive. It focuses on the key requirements, the sectors affected and the steps needed to comply. It serves as a practical guide for businesses to navigate the new cybersecurity landscape and provides insights into the challenges and opportunities of NIS2.
What you need to know about NIS2
The scope of NIS-2 covers 18 sectors, which are divided into two classes.
- The “high criticality sectors” include energy, transportation, banking, financial market infrastructure, healthcare, drinking water, wastewater, digital infrastructure, management of ICT services (B2B), public administration and space.
- The “other critical sectors” include postal and courier services, waste management, chemicals, food, manufacturing, digital service providers and research.
Affected are
- large companies with at least 250 employees or over 50 million euros in annual turnover and over 43 million euros in annual balance sheet total and
- medium-sized companies with 50 to 249 employees or between 10 and 50 million euros in annual turnover or between 10 and 43 million euros in annual balance sheet total.
- small companies are generally not in the direct scope of application, but may be affected by special regulations in the scope of application or via the supply chain.
Major facilities are large companies that fall into one of the “high criticality sectors”. They are subject to regular and targeted safety inspections (ex-ante) and random checks. Important facilities include medium-sized companies from “high criticality sectors” as well as large and medium-sized companies from “other critical sectors”. Here, on-site inspections and external ex-post supervisory measures are only carried out if there are reasonable grounds for suspicion (ex-post).
Affected companies and organizations must take appropriate security measures to ensure the confidentiality, availability and integrity of their networks and IT systems. This includes
- the development of concepts for risk analyses and the security of information systems as well as concepts and procedures for evaluating the effectiveness of risk management measures,
- measures that contribute to the detection and minimization of security incidents,
- ensuring business continuity through backup and crisis management measures,
- measures to ensure the security of supply chains,
- cyber hygiene procedures as well as training, further and advanced training in the area of cyber security,
- the use of cryptography and encryption technology,
- personnel security, access controls and asset management,
- solutions for multi-factor authentication or continuous authentication, and
- the use of secure voice, video and text communication
Once a problem has been identified, it must be reported within 24 hours whether the incident is based on an illegal or malicious act or may have cross-border implications (= early warning).
An initial assessment of the cyber security incident must be submitted within 72 hours.
An interim or final report with a detailed description of the cyber security incident must be submitted one month after the notification.
With NIS 2, the management of a company or management bodies of an organization can be held personally liable. They must ensure and monitor the implementation of and compliance with risk management measures.
Violations of the NIS 2 Act result in high fines:
- For essential facilities, the fine range is up to €10 million or up to 2 percent of global turnover (whichever is higher).
- For important facilities, a fine of up to EUR 7 million or up to 1.4 percent of global turnover (whichever is higher) can be imposed.