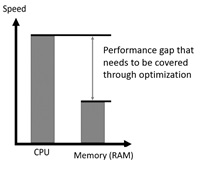
These performance bottlenecks forced CPU manufacturers to develop a variety of different optimization techniques which led to additional layers between the CPU and memory. As a result, two new concepts were introduced:
- Out-of-order execution blocks – an intelligent CPU optimization technique for making smart guesses and anticipating what to do next.
- Processor’s cache (or just cache) – very fast memory with a small storage capacity located very close to the CPU. Only data is stored here.
Out-of-order execution blocks make assumptions by themselves about which data will be needed in the near future by the running process. Based on those decisions, data is simply fetched in advance from memory and stored in cache by the CPU:
- If the assumption turns out to be correct and if the running process has the permissions to access the fetched data, the data is processed.
- In all other cases it is just thrown away by the processor.
The applications and operating system do not have any influence on this behaviour at all. It is all hardcoded in the hardware.
Introduction to Side Channel Attacks
The root cause that is abused by the attacker during the Meltdown exploit
So far, the features described above do not seem to be problematic. However, there are two key issues where things start to go wrong:
- Problem 1: Fetching from memory to cache without checking permissions first. The permissions for accessing the data by the affected CPUs are checked after fetching data from memory to cache.
- Problem 2: Not Deleting Data from Cache. Data stored in cache is not immediately cleaned after checking permissions – even if the permission check failed.
This is the point where a so called side channel opens and starts to leak valuable information to an attacker. By definition, a side channel is an implicit source of information that might be used by an attacker to disclose sensitive data. Side-channel attacks are not new to the IT-security world. Common attacks which were successful in the past were based on changes in power consumption, electromagnetic radiation or timing fluctuations in the system’s performance.
For instance, in March 2008 the KeeLoq system was broken by high-precision measurement of the device’s power consumption during encryption. KeeLoq is a proprietary hardware-dedicated block cipher designed by Microchip Inc. It is used in a variety of remote car and building control systems. As a result, the lock system was completely compromised.