Communication is key, more than ever. With the digital era, companies started to benefit from significant productivity gains and enhanced customer experience at low cost. But what if someone took away your key? What if you wanted to start an important conference call for that desperately needed business venture or your support staff can’t answer clients’ support calls to talk them through delicate bug fixing issues on their computers?
Application Security As A Quality Aspect
A few months ago, the SEC Consult Vulnerability Lab discovered a denial of service (DoS) vulnerability in Skype for Business and Lync 2013. Namely, if one were to send a certain amount of emojis, one could force the recipient’s Skype for Business client to stop working. Our research shows, that a similar issue already occurred in early 2015. Back then, multiple animated emoticons would cause a client’s CPU usage to go through the roof. The issue was resolved within only one patch cycle, which is extremely fast for big software development companies nowadays.
Threat evaluation
With customer service demands higher than ever and companies working in remote teams across the globe, the permanent availability of tools such as Lync and Skype for Business is crucial to pull in sales. In February 2012 (yes that long ago), an amazing 90% of the Fortune-100 and 70% of the Fortune-500 companies were already using Microsoft Lync, also known as Skype for Business. All the call center agents, support staff and remote teams are expected to exceed 100 million enterprise seats by the end of 2018.
Due to the wide-spread use of the program today, a responsible disclosure process with Microsoft was triggered upon and a dedicated patch to fix the vulnerability was issued and included as a security update within Patch Tuesday of November 2018.
How Does The Dos Attack In Skype For Business Work?
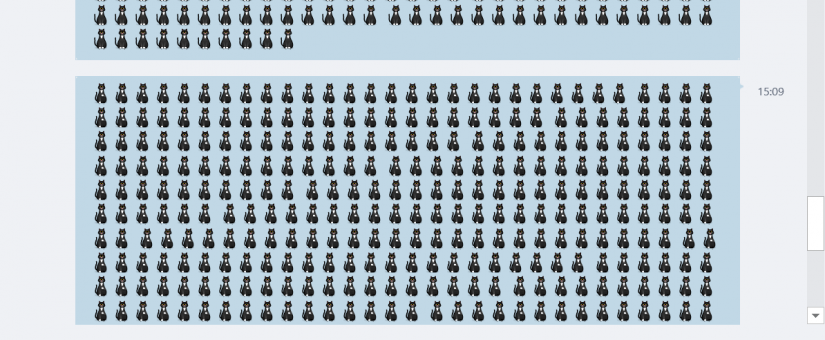
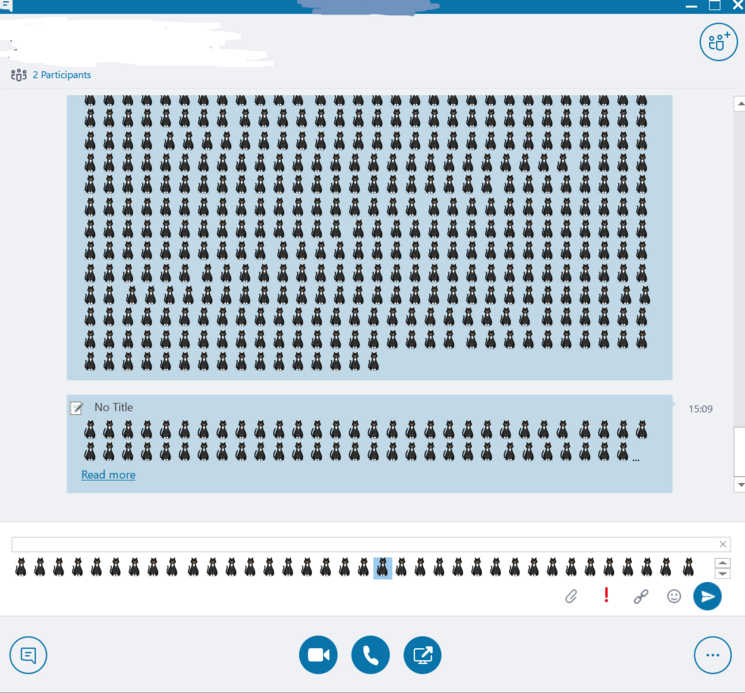
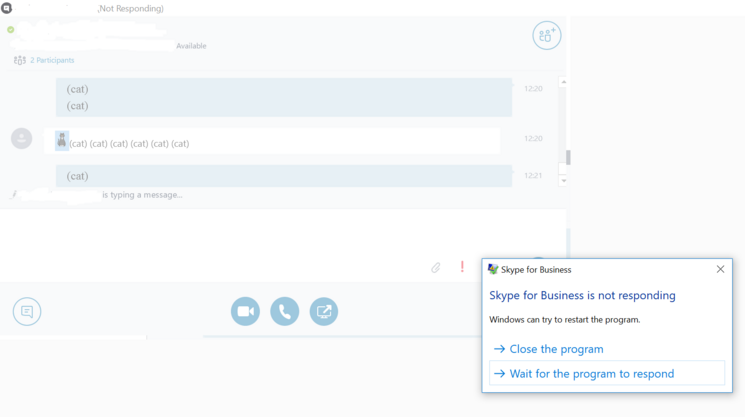
A (malicious) sender invites you to join a meeting or simply contacts you via Skype and sends you a huge amount of emojis, e.g. cute kittens. Depending on the actual amount of kitten emojis, you might notice a short lag in your application (starting with 100 emojis).
When receiving about 800 kittens at once, your Skype for Business client will stop responding for a few seconds. If a sender continues sending emojis your Skype for Business client will not be usable until the attack ends.