Vendor description
"Digital Guardian is proud to be part of Fortra’s comprehensive cybersecurity portfolio. Fortra simplifies today’s complex cybersecurity landscape by bringing complementary products together to solve problems in innovative ways. These integrated, scalable solutions address the fast-changing challenges you face in safeguarding your organization. With the help of the powerful protection from Digital Guardian and others, Fortra is your relentless ally, here for you every step of the way throughout your cybersecurity journey."
Source: https://www.digitalguardian.com/
Business recommendation
SEC Consult recommends users of this platform to install the latest update.
Furthermore, an in-depth security analysis performed by security professionals is highly advised, as the software may be affected from other security issues.
Vulnerability overview/description
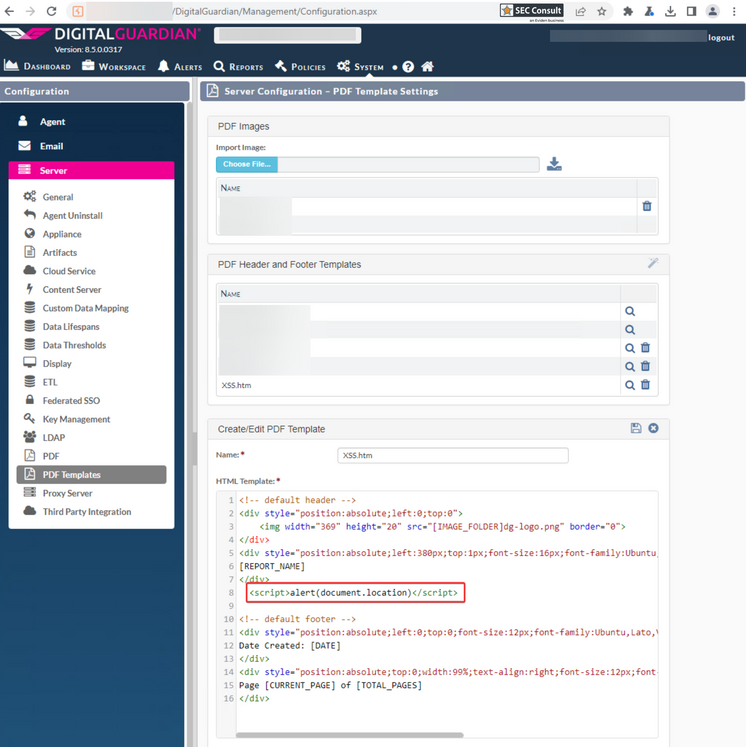
1) Stored Cross-Site Scripting
The "PDF templates" feature is vulnerable against stored cross-site scripting because it allows inserting arbitrary HTML. Therefore, an administrator can create a malicious template which contains JavaScript and can send a link to this template to authenticated users.
According to the vendor, this feature works as intended and the associated risk is low, hence it will not be fixed.
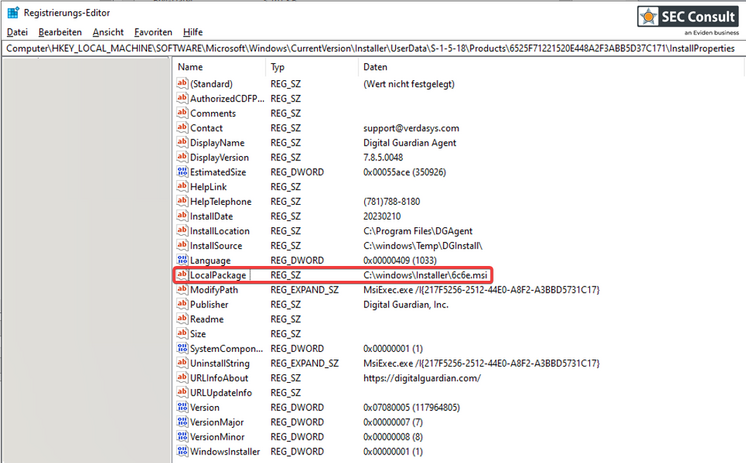
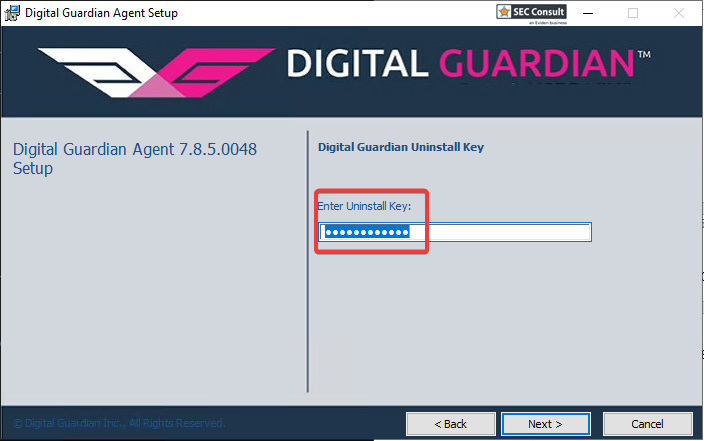
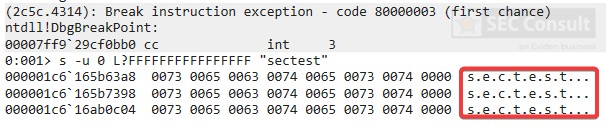
2) UninstallKey Cached in Memory / Installer File (CVE-2023-6253)
The Agent Uninstaller handles sensitive data insecurely and caches the Uninstall key in memory. This key can be used to stop or uninstall the application. This allows a locally authenticated attacker with administrative privileges to disable the application temporarily or even remove the application from the system completely.