Guardians of the Digital Realm: Celebrating 400 Advisories and Responsible Disclosure
news
Launched in the year 2003, in the early days of the Internet's widespread adoption, the Lab's mission was clear:
And what a journey it has been!
The first part of this blog post series honours the contributors of the past two decades of the SEC Consult Vulnerability Lab whereas the second, upcoming part is a more critical reflection on our experience with responsible disclosure, e.g., regarding non-responsive vendors, patches taking multiple years, legal threats and open questions and wishes for the future.
Both blog posts were written by Johannes Greil, Head of SEC Consult Vulnerability Lab.
20 years SEC Consult Vulnerability Lab
The role of ethical hackers has become increasingly important in the ever-evolving world of IT security. These guardians of the digital realm tirelessly probe for vulnerabilities, expose weaknesses, and serve as the unsung heroes of our connected age.
It all started in a small, shared office space in Vienna, Austria in 2002. There were only a handful of IT security specialists in the newly founded security consulting company “SEC Consult”, but the company grew fast into an internationally renowned business. It became apparent quite quickly, that the company’s mission to protect customers’ information assets and make the world a safer place through commitment, expertise, and innovation, could only be achieved by constantly improving ourselves.
One of the possibilities to achieve our goals of being better than world-class, is to nurture a culture of learning and building up knowledge. It was decided that we should also make our findings available to the world, as everyone would profit from the research publications in the same way as we benefit from others in the security community.
The SEC Consult Vulnerability Lab was born.
We started publishing security advisories as early as 2003. Soon, we saw the need for responsible disclosure – at that time full disclosure and sending 0-days to BugTraq or other mailing lists was rather common. Ultimately, we want our customers to be able to patch or reconfigure their systems in a timely manner, provide proof of concept material to the community, or strengthen the detection mechanisms for defenders.
Throughout the past two decades, the Lab has built up a remarkable record of achievements, raising our advisory counter to over 400 published security advisories and even more interactions with vendors. Similarly, an additional three-digit number of advisories with 0-days that could not be made public for a variety of reasons. Many interesting technical blog posts, proof of concept videos, Pwnie award nominations and winnings, multiple talks at conferences such as Black Hat or Hack in the Box, published open source tools, or media articles can be added to the success of the SEC Consult Vulnerability Lab.
But what is the Vulnerability Lab? It is comprised of all our employees who contribute to every publication in one way or another.
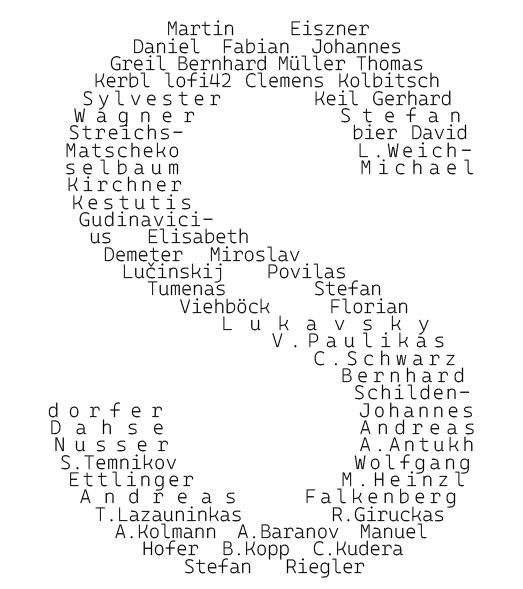
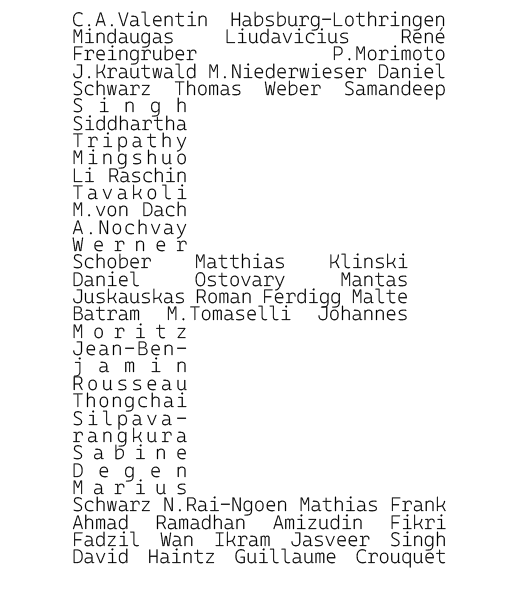
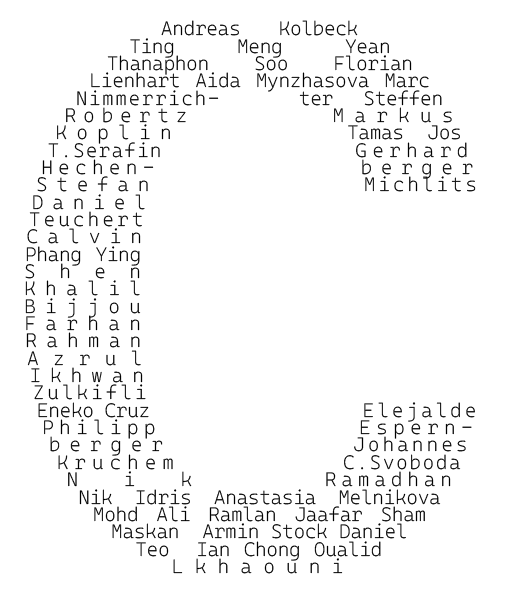
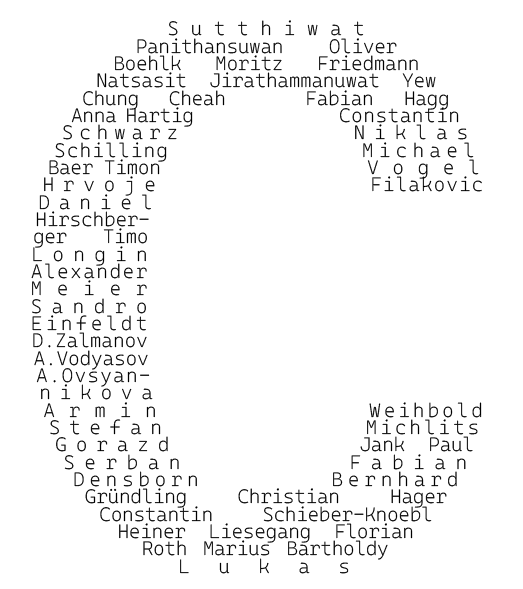
It could not have been possible without the first employees and back then CTO Martin Eiszner and now Google red teamer and senior staff manager Daniel Fabian, eagerly pushing out the first advisories. I also want to thank so many more colleagues I am proud to have worked for in the past decades.
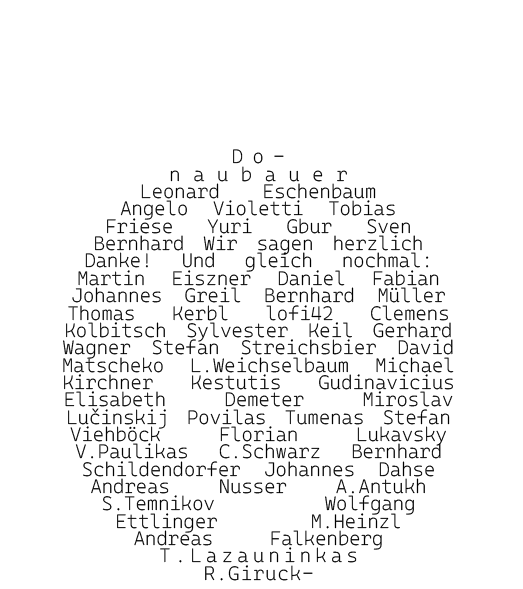
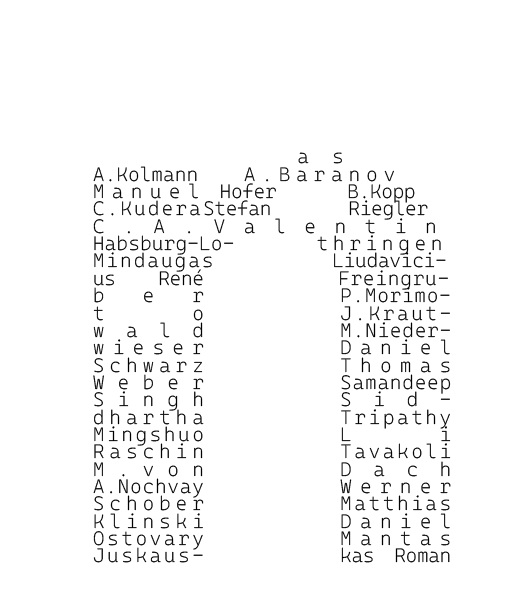
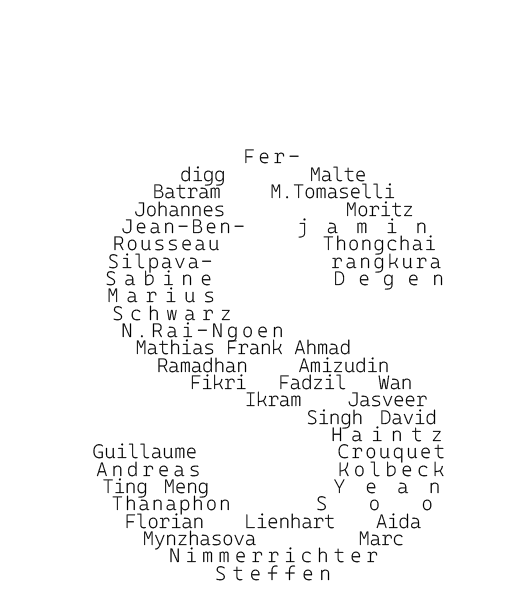
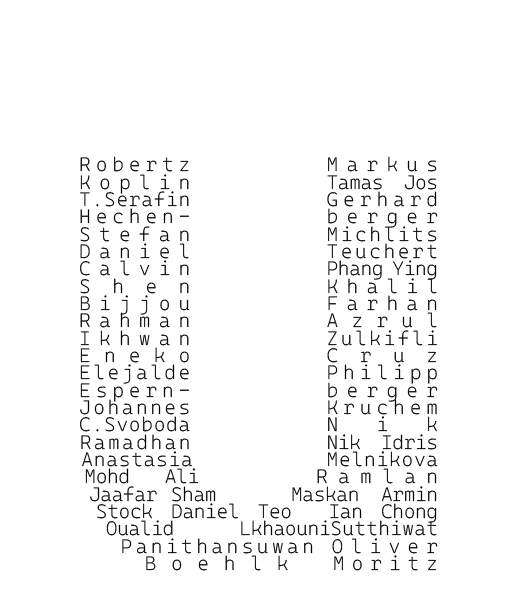
The following overview contains all past and current researchers at SEC Consult who have published a security advisory or blog post, and many more who did not wish to be named in our public security advisories (the order is based on the year and is therefore somewhat random):

Take a closer look:
Publishing security research and advisories is a quadruple win for our stakeholders. The vendors get a quality improvement, SEC Consult customers do not need to bother with vendor coordination and communication, we as a company get some marketing material, and our team gets the CVE (Common Vulnerabilities and Exposure) numbers and deeper expert knowledge.
Yet, it would be remiss not to recognize the hurdles and challenges that have punctuated this journey. Responsible disclosure, a principle at the core of ethical hacking, has not always received the warm embrace it deserves. Our upcoming blog will dig deeper into our experience with responsible disclosure and different types of more or less security-aware vendors.